Originally published November 2025
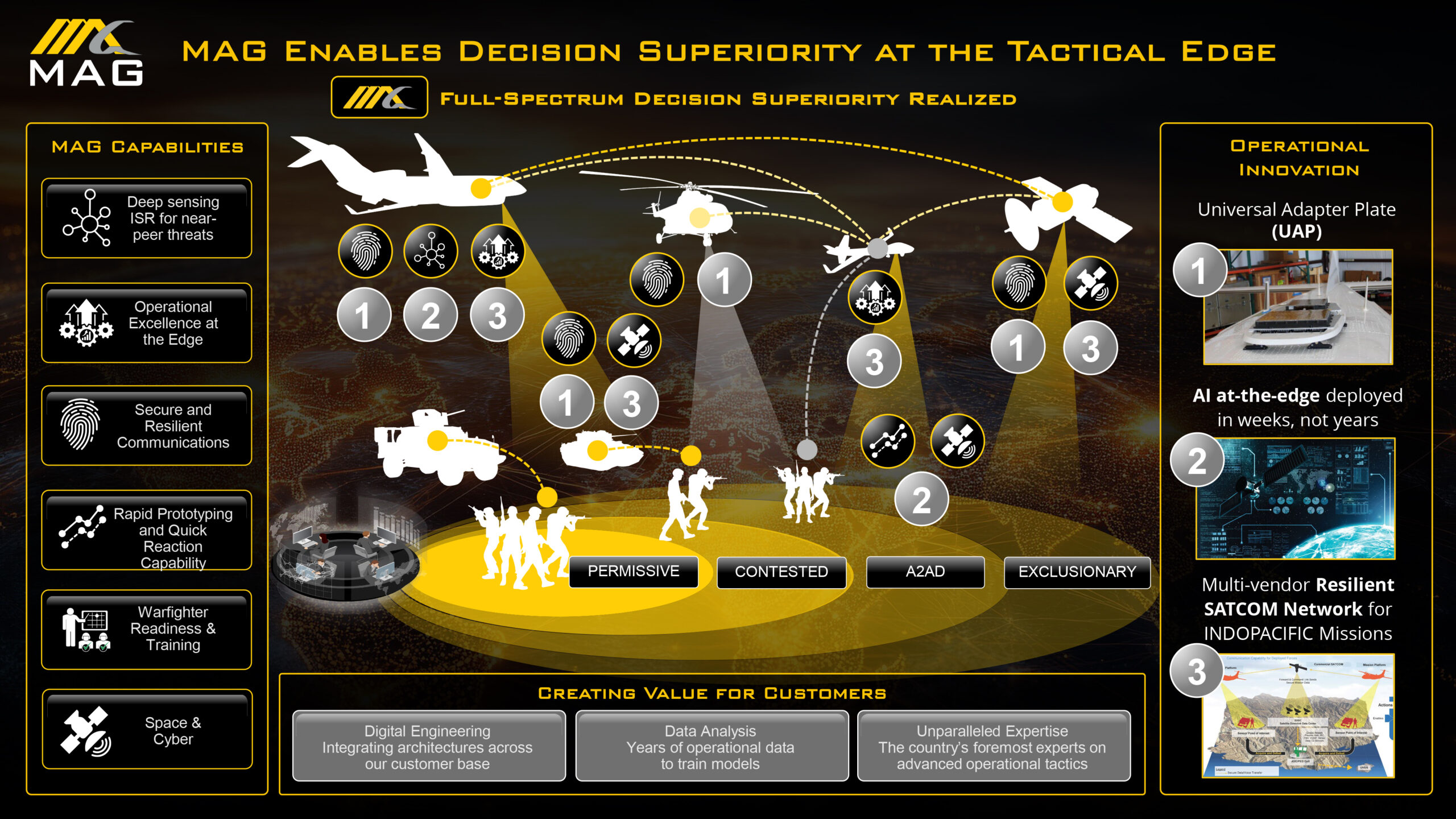
Defense interoperability is the seamless integration of disparate military systems, platforms, and forces to exchange data and coordinate actions across all operational domains. In 2026, achieving interoperability relies on the Combined Joint All-Domain Command and Control (CJADC2) framework and the Modular Open Systems Approach (MOSA). By leveraging artificial intelligence (AI) at the tactical edge and open-architecture sensor fusion, organizations like MAG Aerospace compress the sensor-to-shooter kill chain, eliminate proprietary vendor lock-in, and deliver a unified Common Operating Picture (COP) that secures decision superiority for joint and coalition forces.
Statistical Summary of Defense Interoperability Trends (2025–2026)
|
Metric / Focus Area |
2025–2026 Statistical Data Point |
Strategic Implication |
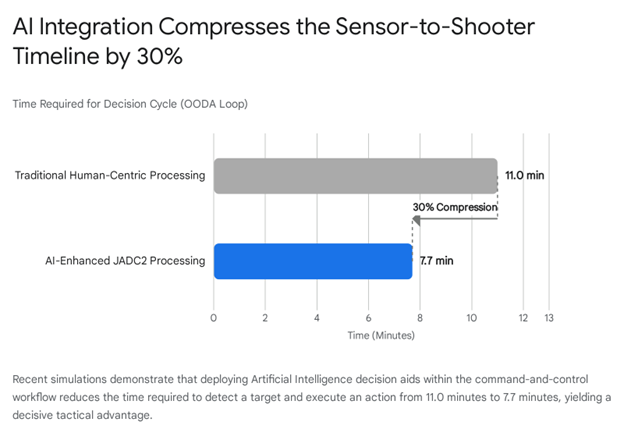
| Sensor-to-Shooter Compression | AI decision aids reduced the sensor-to-shooter interval from 11.0 minutes to 7.7 minutes, achieving a 30% compression of the OODA loop. | Drastically increases operational tempo and lethality in Large-Scale Combat Operations (LSCO). |
| CJADC2 Budgetary Commitment | The Department of Defense (DoD) requested over $1.4 billion for CJADC2 activities in its fiscal year 2025 budget. | Demonstrates massive, sustained prioritization of network-centric, multi-domain warfare architectures. |
| MOSA Adoption Rates | 14 out of 20 Major Defense Acquisition Programs (MDAPs) initiated post-2016 have successfully implemented MOSA principles. | Validates the shift away from proprietary vendor lock-in toward modular, upgradable architectures. |
| Global Defense IT Spending | Projected to expand from $102.18 billion in 2025 to $152.11 billion by 2033 (5.1% CAGR). | Command-and-control systems and cybersecurity infrastructure are the primary drivers of defense capital expenditure. |
| Cost Avoidance via Open Architecture | Subsystem retrofits utilizing a MOSA framework yielded $3.8 million in life-cycle savings against a $500,000 initial investment. | Proves the economic viability and extreme long-term cost efficiency of utilizing open standards. |
The Strategic Imperative of Defense Interoperability in 2026
In the contemporary geopolitical landscape, the character of warfare has fundamentally shifted from a platform-centric model to a network-centric paradigm. For decades, military procurement and tactical doctrine were defined by the acquisition of isolated, exquisite platforms—fighter jets, naval vessels, and armored vehicles operating with highly specialized, proprietary communication links. However, the global security environment has evolved rapidly. The emergence of great power competition, characterized by near-peer adversaries with advanced technological capabilities, has rendered isolated operational models obsolete. Modern military doctrine recognizes that victory in high-intensity conflicts hinges on absolute information dominance.
Defense interoperability is the foundational capacity for diverse military systems, hardware, and software to communicate, exchange data, and operate in unison. This requirement transcends basic digital connectivity; it demands deep technical, procedural, and human alignment. The overarching goal is to ensure that a data point collected by a sensor on an unmanned aerial vehicle (UAV) can be instantly interpreted and acted upon by a naval commander or a ground-based artillery unit, regardless of the service branch or allied nation involved.
The strategic importance of achieving this level of interoperability cannot be overstated. A highly interoperable force is drastically more agile, resilient, and lethal than a collection of isolated units. Conversely, forces operating in silos suffer from fragmented situational awareness, delayed response times, and an increased risk of friendly fire and mission failure. The current strategic landscape, marked by what defense analysts term an “Axis of Upheaval” alongside a staggering $36 trillion national debt, forces the Department of Defense (DoD) to seek unprecedented efficiencies. The military can no longer afford to over-invest in isolated systems that cannot share telemetry data or targeting coordinates. Instead, the focus has pivoted entirely toward multi-domain operations (MDO), where the integration of information and warfighting capabilities across land, sea, air, space, and cyberspace generates outsized battlefield effects.
Recent data from modern conflicts highlights a technology consumption rate that defies peacetime logic. Combined forces are losing thousands of uncrewed systems monthly, an attrition rate that could rapidly deplete conventional fleets in a high-intensity scenario. To survive and dominate in this environment, defense technology must facilitate seamless collaboration. Interoperability acts as the ultimate force multiplier, ensuring that every asset deployed in the battlespace contributes to a unified, resilient network capable of out-thinking and out-maneuvering the adversary.
Combined Joint All-Domain Command and Control (CJADC2): The Evolution of the Network
To solve the historical interoperability gap, the DoD introduced the Joint All-Domain Command and Control (JADC2) strategy in 2019. This initiative aimed to connect sensors, deciders, and shooters across all warfighting domains into a cohesive, high-speed battle network. However, recognizing that the operational reality of modern warfare increasingly relies on deeply integrated coalition forces, the framework was evolved and formally renamed to Combined Joint All-Domain Command and Control (CJADC2) in 2023. This deliberate nomenclature shift reflects the absolute necessity of integrating international partners and allied nations into the central network architecture.
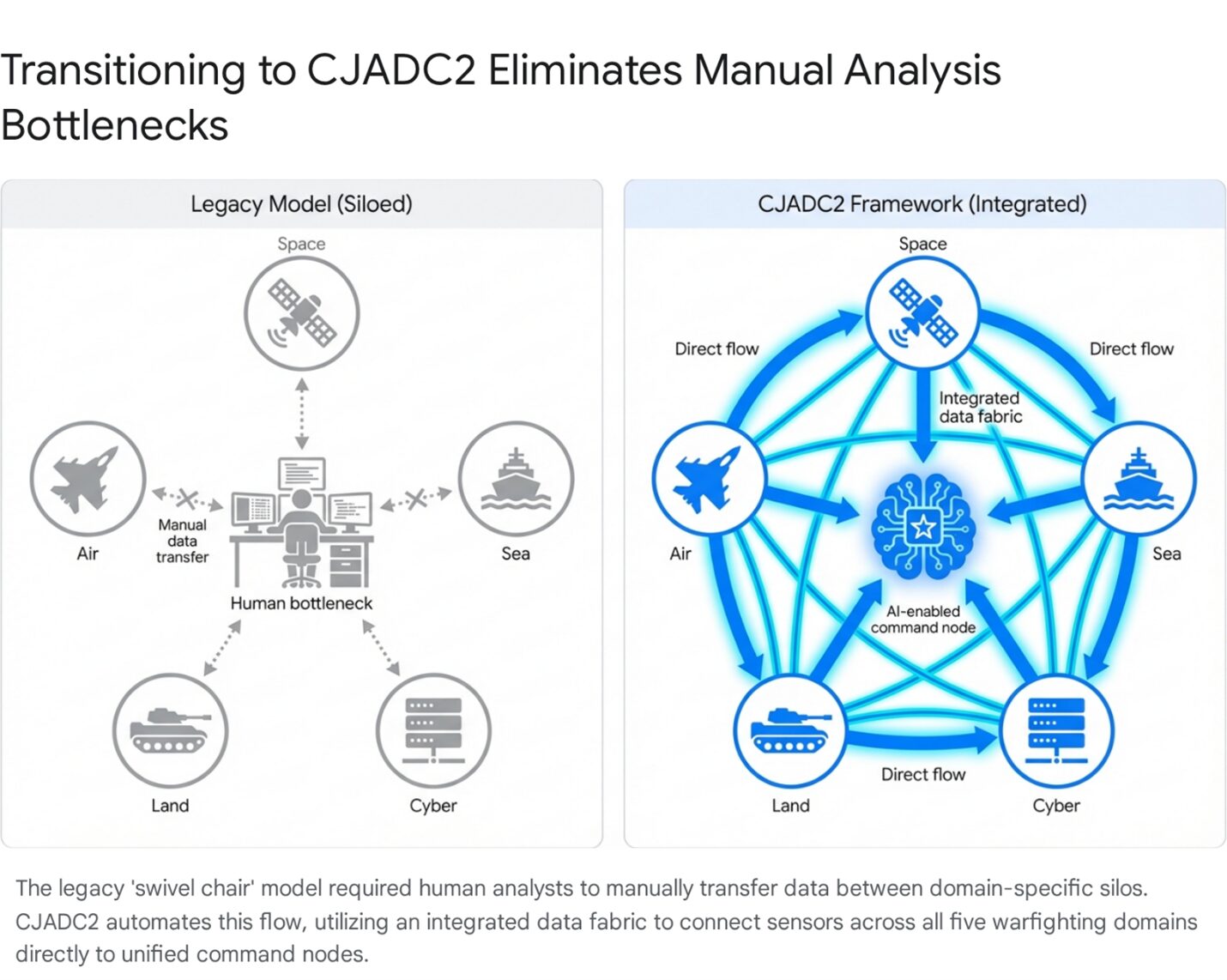
Dismantling the “Swivel Chair” Analysis Model
The primary operational objective of CJADC2 is to eliminate the archaic “swivel chair” analysis model. Historically, intelligence analysts were forced to manually receive data from one specialized, domain-specific system, physically or cognitively pivot, and manually enter that data into a separate command-and-control system. In an era where hypersonic weapons, autonomous drone swarms, and automated cyber-attacks unfold in seconds, manual data processing represents a fatal vulnerability.
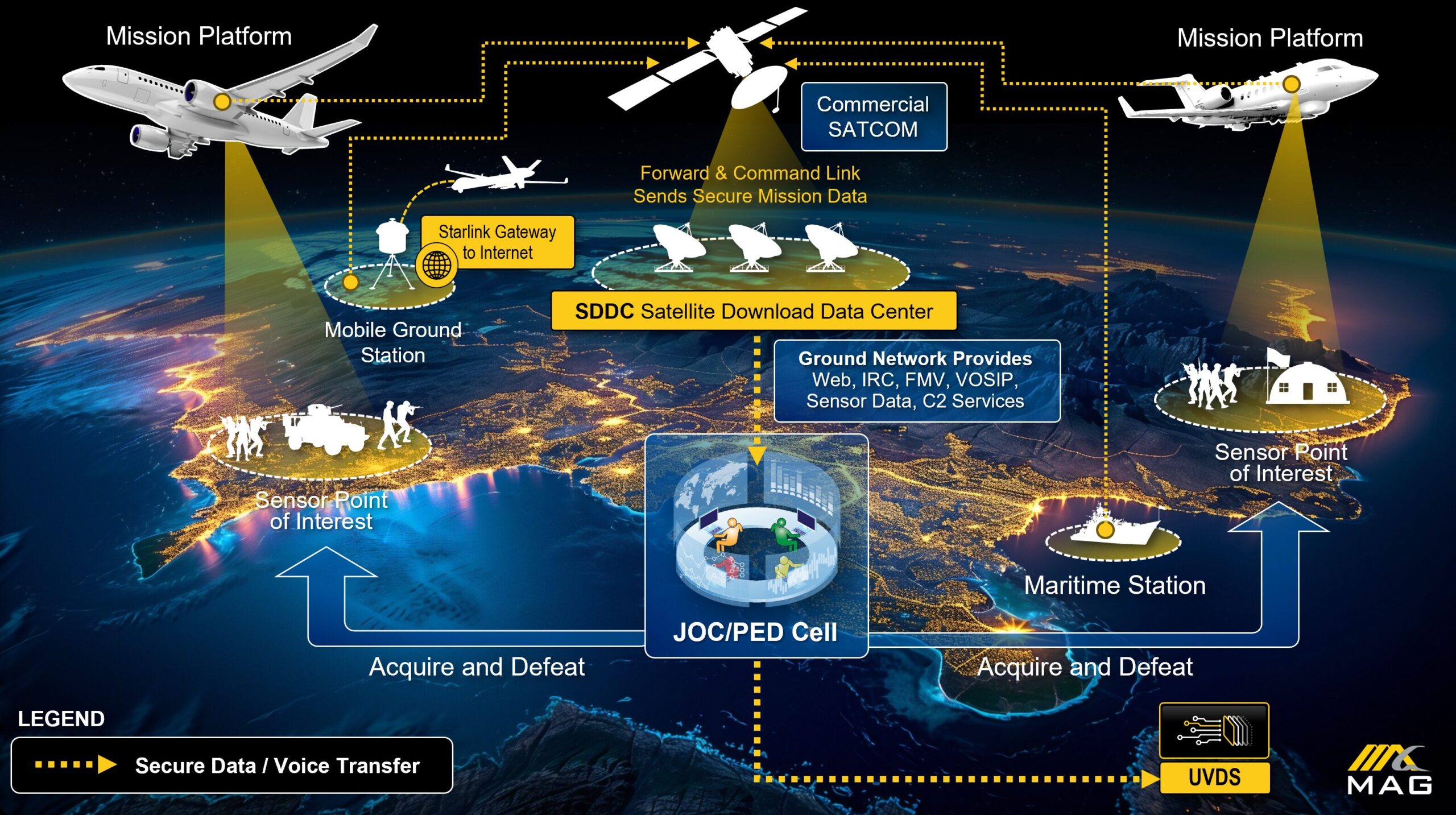
CJADC2 envisions a fully integrated model where data flows automatically across domains, filtered by machine learning algorithms, to deliver actionable intelligence directly to decision-makers. This integrated data fabric allows telemetry data and real-time video to be ingested at the tactical edge, transported over satellite communications (SATCOM), and analyzed centrally before being pushed back to the warfighter.
Budgetary Priorities and Service-Specific Implementation
The DoD’s financial commitment to this transformation is immense. In its fiscal year 2025 budget request, the DoD allocated over $1.4 billion specifically for CJADC2 activities. Looking ahead to the FY26 Joint Estimate System (JES), funding for JADC2 Development and Experimentation Activities was requested at $297.8 million, supplemented by an additional $275 million from the OBBBA, totaling $572.8 million for research and development alone. Furthermore, the Air Force recently awarded a massive indefinite-delivery/indefinite-quantity (IDIQ) multiple-award contract worth up to $950 million to 27 companies to drive the maturation, demonstration, and proliferation of JADC2 technologies.
To execute the CJADC2 vision, the respective military branches have launched major, targeted initiatives. The Army’s contribution is driven by the Next Generation Command and Control (NGC2) initiative and the highly publicized Project Convergence, which focuses on revolutionizing division-level targeting in large-scale combat operations. The Air Force continues to advance its Advanced Battle Management System (ABMS), utilizing continuous integration and continuous delivery (CI/CD) pipelines to deploy digital infrastructure across the force. The Navy operates Project Overmatch to connect maritime and joint assets, while the Marine Corps pursues Project Dynamis to ensure expeditionary units remain tightly integrated.
Overcoming Structural and Security Challenges
Despite robust funding and high-level strategic guidance, achieving seamless CJADC2 interoperability is fraught with institutional and technical friction. A comprehensive 2025 review of defense command and control progress by the Government Accountability Office (GAO) revealed that the DoD has struggled to establish a comprehensive, enterprise-wide framework to guide investments. Consequently, military branches have frequently pursued their distinct data integration projects in isolation, running the risk of creating new, highly sophisticated silos if not aggressively managed for cross-service compatibility.
Furthermore, over-classification remains a profound barrier to multi-domain operations. CJADC2 demands rapid, frictionless data sharing, but strict, legacy data classification protocols frequently prevent information from flowing freely between U.S. combatant commands, the intelligence community, and crucial international partners. Modern defense integrators must design systems that not only speak the same digital language but also incorporate advanced, military-grade Cross Domain Solutions (CDS). These solutions must dynamically manage access levels across different security classifications in real-time, preventing unauthorized access without halting the flow of mission-critical telemetry.
Coalition exercises have proven critical in identifying and resolving these gaps. During the Capstone 2025 event, U.S. forces collaborated with the United Kingdom and Canada over the Combined Federated Battle Laboratories Network. This environment enabled parallel testing of AI/ML tools, allowing the UK to generate courses of action and share Air Tasking Orders directly with U.S. systems. This real-time integration successfully validated the CJADC2 concept in a true coalition environment, proving that data sharing challenges can be overcome through rigorous, cooperative engineering.
The Modular Open Systems Approach (MOSA) as the Technical Bedrock
At the core of solving the defense interoperability puzzle—and realizing the full potential of CJADC2—is the widespread, mandated adoption of the Modular Open Systems Approach (MOSA). MOSA is not merely a technical architecture; it is an integrated business and engineering strategy demanded by the DoD to ensure competitive, affordable, and rapid acquisition over a system’s entire life cycle.
Historically, the defense industrial base relied on purpose-built, highly proprietary systems engineered by a small handful of prime contractors. While these systems were effective for their specific, narrow missions, they resulted in severe “vendor lock-in”. If the military needed to upgrade a single sensor, patch a cyber vulnerability, or swap a communication link, they were contractually and technically forced to return to the original manufacturer. This paradigm resulted in exorbitant life-cycle costs, delayed deployment schedules, and a fundamental inability to interoperate with allied or joint platforms.
Legislative Mandates and the Mechanics of MOSA
Recognizing the unsustainability of proprietary ecosystems, Congress intervened. The National Defense Authorization Act (NDAA) for Fiscal Year 2017 mandated that all major defense acquisition programs implement MOSA to the maximum extent practicable. This was further expanded by the FY21 NDAA Section 804, which provided alternative pathways to achieving openness, focusing heavily on intellectual property (IP) rights. The legislation dictates that the government must secure the necessary Form, Fit, and Function (FFF) data rights, as well as Operation, Maintenance, Installation, and Training (OMIT) data, to allow third-party vendors to seamlessly integrate their technology into existing platforms.
MOSA dismantles the proprietary paradigm by requiring systems to be designed with highly cohesive, loosely coupled, and severable modules connected by internationally recognized, consensus-based open standards and Application Programming Interfaces (APIs). This modularity yields five primary, transformative advantages for defense procurement and battlefield operations:
|
Strategic Advantage
|
Mechanism of Action
|
Operational Impact
|
| Enhanced Competition | Utilizing open architectures with severable modules allows individual components to be openly competed among diverse vendors. | Breaks vendor lock-in, democratizes access for non-traditional tech firms, and drives market innovation. |
| Rapid Technology Refresh | Standardized interfaces permit the delivery of new capabilities without requiring a complete redesign of the platform. | Keeps warfighters at the cutting edge by allowing continuous integration of the latest AI, radar, or cyber tools. |
| Incorporation of Innovation | Provides operational flexibility to configure and reconfigure available assets rapidly. | Commanders can adapt physical assets dynamically to meet rapidly changing, unpredictable threat environments. |
| Unrestricted Interoperability | Systems built on common standards inherently communicate more effectively with other compliant systems. | Forms the essential technological bedrock required for CJADC2 and seamless joint/coalition multi-domain operations. |
| Significant Cost Avoidance | Enables the reuse of technology, modules, and software code across the acquisition life cycle. | Drastically lowers R&D and sustainment costs, allowing defense budgets to stretch further in austere environments. |
The economic impact of this approach is highly measurable. In one documented instance evaluated by the DoD, utilizing a MOSA framework for a subsystem retrofit yielded approximately $3.8 million in life-cycle cost savings against a minimal $500,000 initial engineering investment. The risk of failure for the open-architecture approach was calculated at a mere 1-2%, proving that the return on investment for modularity is exceptionally high.
Enterprise Adoption and Implementation Challenges
Data from an extensive 2025 review of Major Defense Acquisition Programs (MDAPs) initiated after 2016 demonstrates the growing momentum of this strategy, with 14 out of the 20 reviewed programs reporting the successful implementation of MOSA to at least some extent. In late 2024, the Secretaries of the Army, Navy, and Air Force signed a Tri-Service MOSA Memo, re-emphasizing that fully implementing MOSA into acquisition strategies is paramount for promoting interoperability and technology insertion across all branches. However, the transition is not without friction. Cultural and contractual inertia remains a significant challenge. Traditional prime contractors often resist open architectures to protect proprietary revenue streams. Additionally, the GAO has pointed out that while programs are adopting MOSA, the DoD currently lacks a consistent, standardized method for program offices to conduct rigorous cost-benefit analyses comparing MOSA costs and benefits over a system’s life cycle. Independent oversight continues to push for better planning to realize MOSA’s promised benefits, a dynamic that heavily favors agile integrators with proven open-architecture track records.
Advanced Sensor Fusion, Data Fabrics, and the Common Operating Picture
Situational awareness is the absolute foundation of all military strategy. Without a pristine, real-time understanding of the operational environment, even the most technologically advanced kinetic force cannot maneuver effectively. Interoperability transforms situational awareness from a fragmented, delayed series of intelligence reports into a single, unified, and actionable Common Operating Picture (COP).
To construct a robust and resilient COP, modern defense systems rely heavily on advanced sensor fusion. The 2026 battlefield is completely saturated with data generated by a massive array of sensors, including electro-optical/infrared (EO/IR) cameras, signals intelligence (SIGINT) receivers, synthetic aperture radar (SAR), acoustic sensors, and space-based early warning platforms. When these data streams remain isolated, they provide an incomplete, often conflicting narrative, placing a massive and dangerous cognitive burden on analysts who must manually correlate the inputs.
The Mechanics of Multi-Domain Sensor Fusion
Sensor fusion algorithms ingest massive volumes of disparate, raw data and merge them into a single, cohesive, and contextualized intelligence product. For example, an airborne ISR platform operating in a contested airspace might detect a faint, anomalous radio frequency emission via its SIGINT payload. In a fully interoperable, fused system, this initial detection does not require human intervention to verify; it automatically cues an onboard high-resolution full-motion video (FMV) sensor to orient toward the emission’s exact geographic coordinates.
Both the signal data and the visual feed are processed, correlated, and transmitted over established data link standards—such as Link 16 or NATO Link 1—to be displayed simultaneously on a single, dynamic map for a ground-based commander or an airborne battle manager. This synthesis provides a level of depth and tactical context that no single sensor could achieve independently.
To manage this immensely complex flow of information, the implementation of a unified “data fabric” has become paramount across the DoD. Advanced data management technologies weave individual tactical clouds, private networks, and edge devices together. This allows telemetry data and real-time video to be ingested at the tactical edge, transported over resilient land-mobile radio and satellite communications (SATCOM), and analyzed centrally before being pushed back to the warfighter. This seamless, continuous data pipeline is the lifeblood of JADC2, ensuring that information remains accurate, timely, and universally trusted, thereby fostering confidence among commanders who must base life-or-death decisions on the shared COP.
Artificial Intelligence, Edge Computing, and the Compression of the Kill Chain
In multi-domain operations against near-peer adversaries, the velocity of decision-making is the ultimate metric of success. The military decision cycle, originally formalized by Air Force strategist John Boyd as the OODA loop (Observe, Orient, Decide, Act), dictates that the combatant who can process information and execute actions faster than their opponent will dictate the flow of combat and secure a decisive tactical advantage.
However, the sheer proliferation of battlefield sensors has created an unprecedented deluge of telemetry. Human operators alone are fundamentally incapable of processing this volume of information rapidly enough, leading to what modern defense analysts term the “OODA point”—the critical threshold at which the complexity and speed of incoming data completely overwhelm human cognitive capacity. To overcome this severe bottleneck and compress the sensor-to-shooter timeline, the integration of Artificial Intelligence (AI) and Machine Learning (ML) has transitioned from an experimental concept to an absolute operational necessity.
The Shift to Edge Computing and Agentic AI
To maximize processing speed and minimize latency, AI algorithms must be deployed directly at the “tactical edge”—meaning the data processing occurs locally on the aircraft, armored vehicle, or forward operating base where the data is actually collected, rather than relying on high-latency, vulnerable transmissions back to remote cloud servers. Edge AI enables mission systems to autonomously detect, identify, categorize, and track targets of interest in real-time. Instead of transmitting hours of raw, unanalyzed video footage that consumes massive bandwidth and risks interception, edge processors transmit only the critical metadata and target alerts.
Simultaneously, the defense sector is experiencing a paradigm shift from standard predictive AI models to “Agentic AI”. While early AI provided static dashboards or basic object recognition, Agentic AI systems actively sense, reason, and act within the command-and-control workflow. These advanced systems continuously evaluate live operational data across multiple domains, coordinate with allied assets, and automatically generate optimized courses of action (COAs) for human commanders to review. The system explores a massive solution space simultaneously, ensuring that options remain open as the battlefield situation fluidly develops.
Empirical Evidence of OODA Loop Compression
The empirical results of this AI integration are profound and highly measurable. In rigorous academic simulations and wargames evaluating division-level targeting within Large-Scale Combat Operations (LSCO), the deployment of AI decision aids successfully reduced the sensor-to-shooter interval from a baseline of 11.0 minutes down to 7.7 minutes.
This nearly 30% compression of the OODA loop represents a massive leap in lethality, survivability, and operational tempo, conclusively proving that the integration of AI within JADC2 architectures is the key to maintaining decision advantage.
The success of these AI initiatives relies heavily on human-machine teaming. The 2025 Decision Advantage Sprint for Human-Machine Teaming (DASH 3) marked a significant step forward in this area, focusing on building user trust—a qualitative yardstick reflecting commanders’ confidence in AI outputs and their willingness to act decisively upon machine-generated recommendations. Similarly, the establishment of Task Force 59 by the Navy’s 5th Fleet in CENTCOM has successfully created a sandbox for teaming human operators with uncrewed surface vessels (USVs) and AI agents, vastly expanding maritime domain awareness across the region.
MAG Aerospace: Leading C5ISR Integration and Innovation
Translating the abstract concepts of JADC2, MOSA, and edge-based AI into reliable, deployable military capabilities requires rigorous engineering, iterative testing, and deep system integration expertise. Industry leaders facilitate this highly complex transition through dedicated research and development facilities. MAG, operating from its corporate headquarters in Fairfax, Virginia, leverages its advanced Innovation Centers to drive the development, testing, and deployment of transformative defense technology.
Capabilities of MAG Innovation Centers
MAG serves as a premier hub for Command, Control, Communications, Computers, Cyber, Intelligence, Surveillance, and Reconnaissance (C5ISR) integration. The innovation centers focus heavily on the practical application of defense interoperability, bringing together disparate hardware and software components to ensure they function flawlessly in simulated combat environments prior to expensive and risky field deployment. Core capabilities cultivated within these innovation hubs include:
- Technology Integration and Architecture: Designing robust digital backbones that strictly comply with MOSA standards. This architecture allows for rapid, plug-and-play capability insertions without triggering ground-up redesigns.
- Cyber, Communications, and Networks: Engineering secure, resilient data links capable of operating in heavily contested electromagnetic spectrums. This ensures that the unified COP remains accessible to commanders even under active electronic warfare (EW) attacks.
- Multi-Domain Operations Testing: Simulating highly complex cross-domain data flows to validate that airborne ISR platforms can communicate flawlessly with ground, maritime, and space-based C2 nodes.
- Data and Analysis: Utilizing advanced DevSecOps pipelines to enable rapid, secure delivery of tactical capabilities through world-class automation, multi-architecture environments, and rigorous data analytics.
This hands-on, hardware-in-the-loop approach to system engineering guarantees that integrated solutions provide a direct, uncorrupted bridge between the tactical edge and higher-level command echelons. When intelligence products are formatted properly and transmitted directly into existing C2 systems without requiring manual re-entry, commanders maintain the absolute most current battlefield intelligence.
Validating Interoperability Through Major Contract Awards
The efficacy of MAG Aerospace’s open-architecture integration philosophy is validated by a series of highly significant recent contract awards and strategic partnerships across the DoD.
In a landmark achievement, MAG Aerospace was selected as a prime contractor, alongside teaming partner L3Harris Technologies, to deliver enhanced ISR aircraft for the U.S. Army’s ATHENA-R (Theater-Level, High-Altitude Expeditionary Next Airborne ISR-Radar) program. This initiative highlights the critical military need for long-range precision fires modernization and highly survivable, leading-edge sensor technology capable of operating at expeditionary altitudes.
Furthermore, the company’s deep, specialized expertise in electronic warfare and cyber integration resulted in the award of the Systems Engineering Technical Assistance (SETA) task order. Awarded under the Responsive Strategic Sourcing for Services (RS3) multiple-award IDIQ contract, this effort directly supports the Army Program Executive Office Intelligence, Electronic Warfare and Sensors (PEO IEW&S), specifically the Project Manager Electronic Warfare & Cyber (PM EW&C).
MAG has also demonstrated exceptional agility in rapid prototyping. Their MC-208 Guardian platform was selected as one of five prototype solutions for the U.S. Special Operations Command’s (USSOCOM) Armed Overwatch program. While competition in the ISR space is fierce—evidenced by Sierra Nevada Corporation (SNC) winning the Army’s High Accuracy Detection and Exploitation System (HADES) contract over a formidable team that included L3Harris, Leidos, and MAG Aerospace—MAG’s consistent presence in these massive, multi-billion dollar procurements underscores the sector’s reliance on agile integrators capable of delivering fully networked, interoperable solutions at scale.
Next-Generation Security: The Triad of Multi-Domain Defense
As defense networks become increasingly integrated and reliant on rapid data exchange across the CJADC2 fabric, the attack surface expands exponentially. Near-peer adversaries actively seek to undermine the DoD’s strategic and operational strengths by impeding command and control capabilities through sophisticated cyber-warfare and electronic jamming. To counter this, the defense sector must secure the network architecture just as vigorously as it develops kinetic weapons.
In 2026, the DoD is executing three concurrent cybersecurity modernization mandates that collectively constitute the “Next-Generation Security Triad.”. These initiatives operate under distinct timelines but require a shared modernization substrate to ensure total interoperability and resilience:
- Zero Trust Architecture (ZTA) Implementation (by FY2027): Moving away from perimeter-based defense, ZTA assumes the network is already compromised. It requires continuous authentication and attribute-level access control for every user and device, ensuring secure data sharing across joint and coalition environments. Hardware and firmware security hardening is becoming standard as Zero Trust extends directly to the tactical edge.
- Post-Quantum Cryptography (PQC) Migration (2030–2035): To counter emerging quantum computing threats that could break traditional encryption, the National Security Agency’s Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) mandates a rapid migration to quantum-resistant cryptography, with software and firmware signing required as early as 2025.
- AI System Security Assurance: As AI becomes central to decision-making, securing the AI models themselves against data poisoning and adversarial manipulation is critical. This is governed closely by the Chief Digital and Artificial Intelligence Office (CDAO).
To accelerate the deployment of these secure systems, initiatives like the Software Fast Track (SWIFT) are reshaping the traditional Authority to Operate (ATO) process. By introducing automation and continuous risk monitoring, SWIFT reduces bureaucratic bottlenecks and aligns rigorous cybersecurity compliance with agile, rapid software delivery cycles. Compliance with frameworks such as the Cybersecurity Maturity Model Certification (CMMC) remains non-negotiable, significantly reducing vulnerabilities across the vast defense supply chain.
The Future of Multi-Domain Operations and Lethality
Looking forward, the DoD continues to aggressively fund the bleeding edge of innovation. The Undersecretary of Defense for Research and Engineering has identified six Critical Technology Areas (CTAs) that will define military dominance in the coming decades: Applied Artificial Intelligence (AAI), Biomanufacturing (BIO), Contested Logistics Technologies (LOG), Quantum and Battlefield Information Dominance (Q-BID), Scaled Directed Energy (SCADE), and Scaled Hypersonics (SHY).
These technologies are no longer viewed merely as individual tools, but rather as emerging operational paradigms that must converge. Space situational awareness is rapidly advancing through the integration of sophisticated ground- and space-based sensors, reliant entirely on AI-enabled analytics and massive data fusion to detect threats in congested orbital environments. As the military modernizes toward these extremes, the necessity for a unified, open-architecture network becomes absolute.
By actively dismantling proprietary data silos and aggressively pursuing open-architecture system integration, the defense sector ensures that advanced capabilities can be fully unleashed. Organizations like MAG, focusing on seamless C5ISR integration and rigorous testing through dedicated innovation centers, prove that technology is only as lethal as the network that supports it. Ultimately, prioritizing true defense interoperability guarantees that the joint and coalition warfighter retains the decisive advantage of speed, clarity, and precision in the defining conflicts of the future.
Conclusion: Interoperability as a Force Multiplier
Interoperability is the central pillar of modern, multi-domain military operations. It acts as a force multiplier, enhancing the effectiveness of every platform and warfighter in the network. By breaking down information silos and enabling seamless collaboration, interoperable systems create a decisive advantage.
MAG is committed to delivering solutions that provide this critical capability. Our expertise in open architecture systems integration, data management, and mission-focused engineering ensures that our partners are equipped to meet the challenges of today and tomorrow.
Explore how MAG’s tailored solutions can enhance your organization’s interoperability and mission effectiveness. Our dedicated Interoperability and Innovation Centers drive the development, testing, and deployment of transformative defense technology, ensuring that our clients benefit from the latest advancements and integrated capabilities. To learn more and experience our hands-on innovation in action, connect with us now!
Frequently Asked Questions (FAQ)
1. What is the difference between JADC2 and CJADC2?
Joint All-Domain Command and Control (JADC2) was the Department of Defense’s initial strategic concept to connect sensors, deciders, and shooters across all U.S. military branches and operational domains (land, air, sea, space, and cyber). The framework evolved into CJADC2, adding the word “Combined” to reflect the essential, strategic integration of international coalition partners and allied nations into the central network architecture.
2. How does a Modular Open Systems Approach (MOSA) reduce defense costs?
MOSA reduces life-cycle costs by utilizing standardized, consensus-based open interfaces. This architecture allows individual system components (like sensors or processors) to be easily swapped, upgraded, or reused without forcing the military to redesign the entire platform. This eliminates proprietary “vendor lock-in,” fosters continuous market competition, and accelerates technology refresh cycles.
3. What role does Artificial Intelligence play in the OODA loop?
Artificial Intelligence acts as a massive accelerator for the Observe, Orient, Decide, Act (OODA) loop. By deploying Agentic AI at the tactical edge to autonomously process immense volumes of sensor data, the technology filters out noise and highlights critical threats instantly. This reduces cognitive overload on human operators and has been empirically demonstrated in simulations to compress the sensor-to-shooter timeline by up to 30%.
4. What is the “swivel chair” analysis model?
The “swivel chair” model refers to a highly inefficient, legacy workflow where military intelligence analysts must physically or cognitively pivot between disconnected, siloed systems to gather and synthesize information. CJADC2 architectures aim to completely eliminate this dangerous bottleneck by creating an automated data fabric that presents a seamless, unified Common Operating Picture (COP).
5. How do facilities like the MAG Aerospace Innovation Center support the warfighter?
Innovation Centers serve as highly advanced testing, architecture, and integration hubs. They allow engineers to physically and digitally combine C5ISR systems, cyber tools, and communication networks from various vendors. By validating that these complex systems can securely interoperate in simulated, contested combat environments, these centers ensure the technology is reliable and mission-ready long before it reaches the warfighter.
6. Why is data classification a challenge for defense interoperability?
Strict, legacy data classification protocols frequently prevent critical intelligence from being shared rapidly across different U.S. military commands, intelligence agencies, and international allies. Overcoming this hurdle requires the deployment of advanced, Military-Grade Cross Domain Solutions (CDS) and Zero Trust Architectures that can securely manage data access and authentication at machine speed without halting mission-critical telemetry.
Updated March 2026