By MAG’s Chief Technology Officer – Justin Janaskie
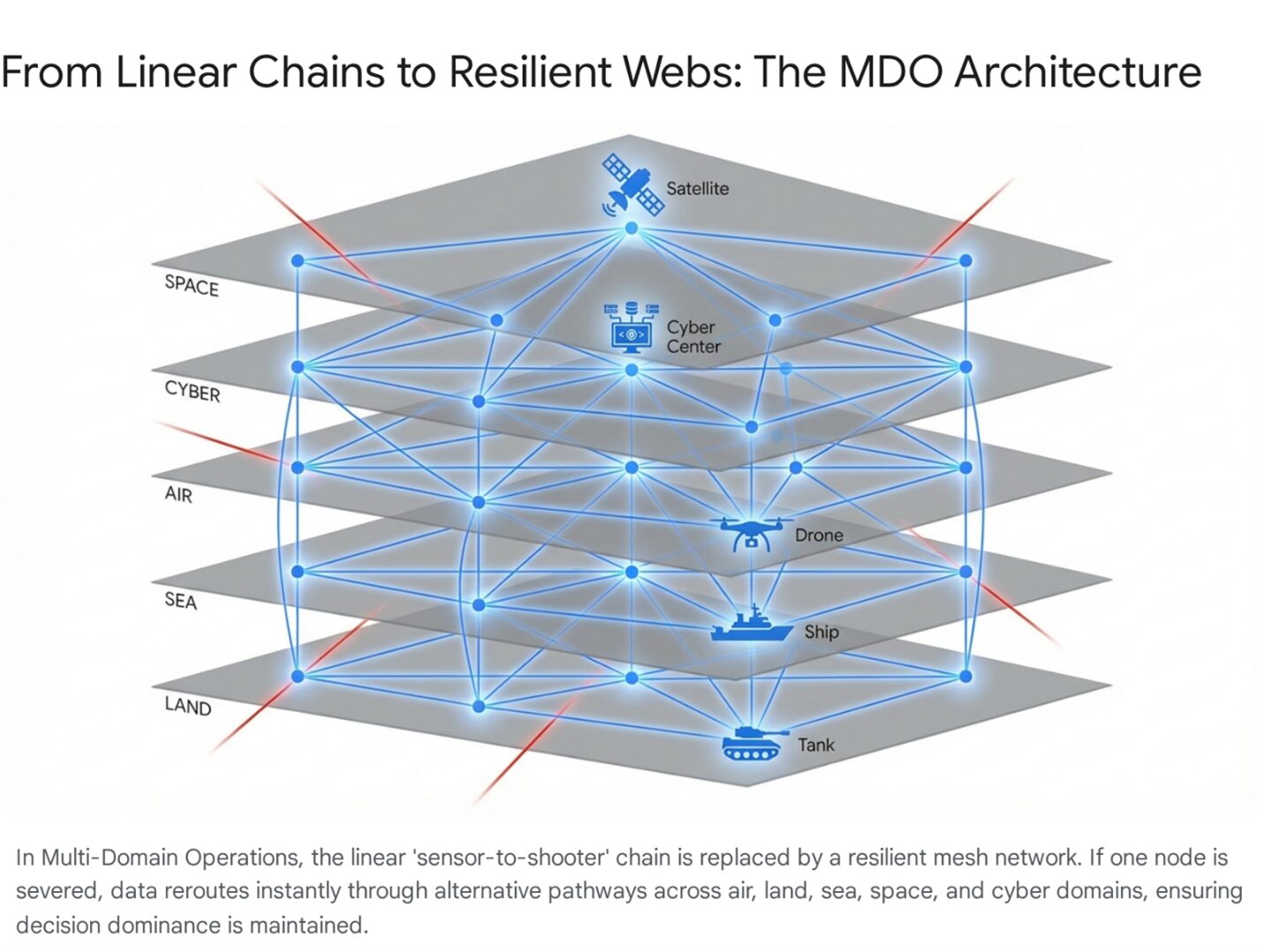
Modern defense requires operating seamlessly across air, land, sea, space, and cyberspace. This complex environment, known as Multi-Domain Operations (MDO), demands more than just superior firepower; it requires decision dominance. The side that can observe, orient, decide, and act (OODA) faster and more effectively will have the decisive edge. Emerging disruptive defense technologies are the engine driving this new reality, transforming how information is gathered, processed, and acted upon. This advanced defense technology is a fundamental shift in operational capability.
This article explores the key disruptive defense technologies shaping the future of MDO. We will examine how artificial intelligence, unmanned systems, cyber tools, and directed-energy weapons are converging to create a faster, smarter, and more integrated common operational picture. Understanding these tools is essential for grasping the future of global security and defense strategy. Furthermore, as we look toward the future battlefield, this article will explore how industry leaders like MAG are engineering the “digital glue” that binds these systems together, transforming raw sensor data into actionable intelligence at the speed of relevance.
The Role of AI and Machine Learning in Defense Technology
Artificial intelligence (AI) and machine learning (ML) are at the core of achieving decision dominance. The sheer volume of data generated in a multi-domain environment is too vast for human analysts to process in real time. AI algorithms can sift through immense datasets from satellites, sensors, and drones in seconds, identifying patterns and threats that would otherwise go unnoticed.
This capability moves defense technology from a reactive to a predictive posture. Instead of responding to an adversary’s actions, AI-powered systems can anticipate them. For example, ML models can analyze an opponent’s troop movements, communication patterns, and logistical activities to predict their next course of action. This is done with a high degree of accuracy. This foresight allows commanders to position assets and prepare responses before a threat fully materializes, seizing the initiative.
Unmanned Systems: The Force Multipliers of MDO
Unmanned systems, including drones and autonomous vehicles, are critical assets in multi-domain operations. They extend the reach of human warfighters, allowing them to project power and gather intelligence without putting personnel at risk. In MDO, not only are these systems valuable reconnaissance tools, but they are also interconnected in a larger information network.
Swarms of low-cost, autonomous drones can work together to overwhelm an adversary’s defenses or create a comprehensive, real-time map of a contested area. Unmanned maritime vessels can patrol vast ocean expanses for weeks, tracking submarine activity or monitoring shipping lanes. This defense technology provides persistent surveillance and a distributed sensor network that is resilient and difficult to counter. When integrated with AI, these unmanned systems can perform complex missions with minimal human intervention, freeing up commanders to focus on strategic decisions.
Maritime Autonomy
In the maritime domain, unmanned systems are addressing the sheer vastness of the ocean, which remains a challenging environment for surveillance. Unmanned Surface Vessels (USVs) and Unmanned Underwater Vehicles (UUVs) offer the ability to patrol shipping lanes, monitor submarine chokepoints, or conduct mine countermeasures for months at a time without the fatigue or logistical support required by human crews.
These systems act as persistent sensor pickets, extending the acoustic and radar horizon of the naval fleet. A network of solar-powered USVs can form a “picket fence” across a strategic strait, detecting the acoustic signature of passing submarines and relaying that data via satellite to a distant command center. This distributed sensor network is resilient; losing one node does not blind the fleet, and the cost of the unmanned vessel is a fraction of the cost of a destroyer or frigate.
Counter-UAS (C-UAS): The Necessary Corollary
The proliferation of unmanned systems by adversaries necessitates a robust Counter-UAS (C-UAS) capability. If swarms are the sword, C-UAS is the shield. Defense technology is rapidly evolving from kinetic solutions—shooting drones with guns or missiles—to non-kinetic solutions.
Electronic warfare plays a primary role here. “Jamming” the command link between a drone and its operator, or “spoofing” its GPS signal to make it crash or land, are preferred methods because they are low-cost and cause minimal collateral damage. However, as autonomous drones become less reliant on external links (using onboard AI for navigation), jamming becomes less effective. This drives the need for “hard kill” options that are cost-effective, such as Directed-Energy Weapons.
Directed-Energy Weapons: A New Frontier
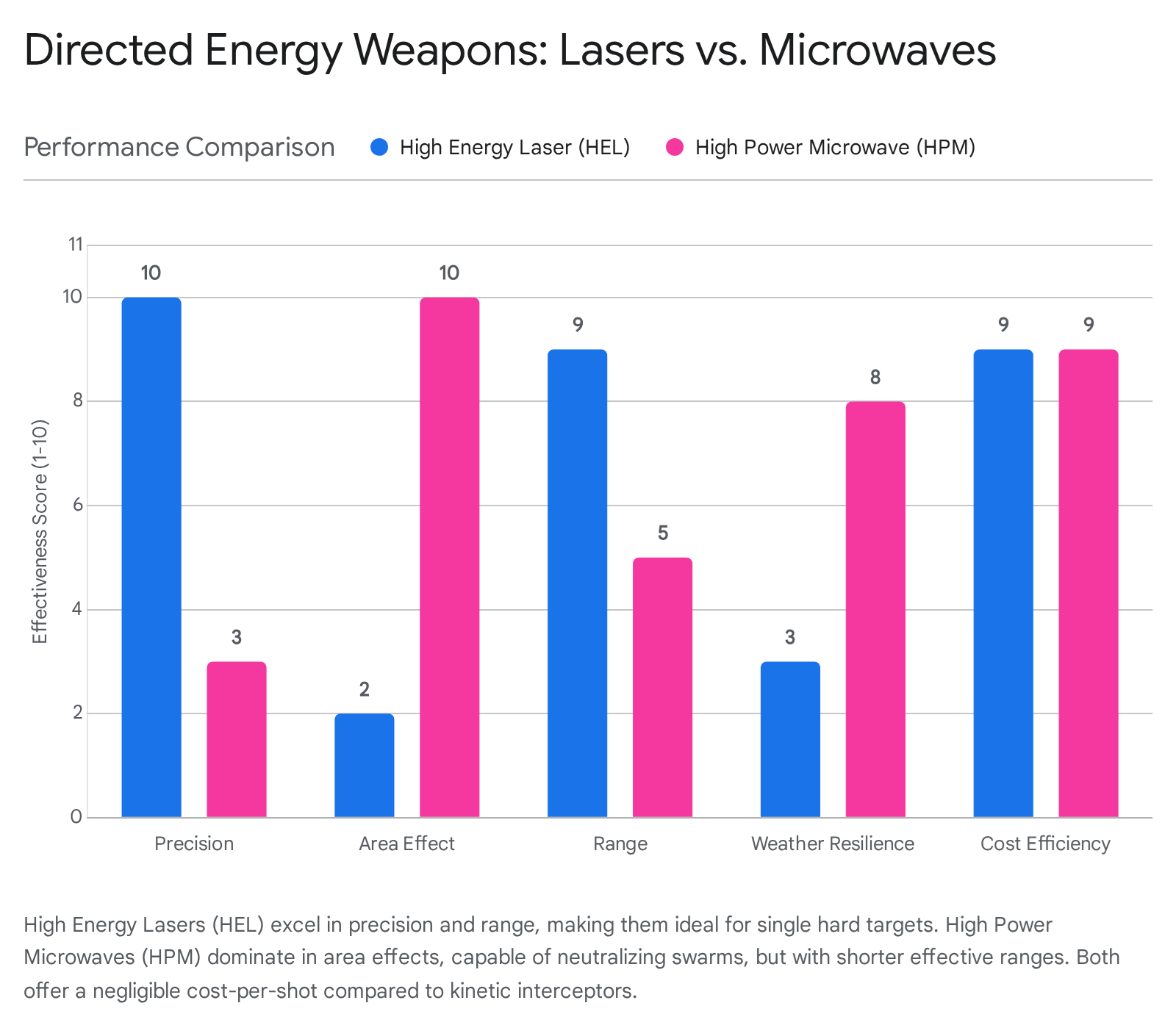
Directed-energy weapons (DEWs) represent a revolutionary step in defense technology. These systems use focused energy, such as lasers or high-powered microwaves, to disable or destroy targets with surgical precision. Unlike traditional munitions, DEWs offer several unique advantages. They have nearly unlimited magazines as long as power is available, and their effects can travel at the speed of light.
In MDO, directed-energy weapons provide a new layer of defense against fast-moving threats like hypersonic missiles and drone swarms. A high-energy laser system can engage multiple targets in rapid succession, offering a more effective solution than single-use interceptor missiles. Furthermore, DEW systems can be scaled to deliver non-lethal effects, such as disabling a vehicle’s electronics without destroying it. This flexibility gives commanders more options and helps reduce collateral damage. As this technology matures, it will become an indispensable part of a multi-layered defense architecture.
Cyber Tools as a Key Domain of Defense Technology
Cyberspace is a distinct operational domain, and the tools used within it are powerful disruptive technologies. Cyber warfare is no longer confined to disrupting websites or stealing data. In an MDO context, cyber tools are used to degrade an adversary’s ability to command and control their forces. This can involve disabling communication networks, corrupting sensor data, or deploying malware to interfere with weapon systems.
In multi-domain operations, cyberspace and the electromagnetic spectrum (EMS) are inextricably linked. The modern battlefield is a digital entity; every radio transmission, every radar pulse, and every data packet exists within the EMS. A radio jamming signal (EW) is an electromagnetic effect, but it disrupts the data transport layer of the cyber network. Conversely, a cyber-attack can inject malware into a radar system, causing it to misinterpret electromagnetic signals. This convergence is known as Cyber-Electromagnetic Activities (CEMA).
The integration of cyber effects with physical operations is a hallmark of modern MDO. A cyber-attack could blind an enemy’s air defense radar just moments before a friendly aircraft enters the airspace. This synchronization of effects across domains creates windows of opportunity and strategic advantages. Effective cyber defense technology is equally important, as it protects the integrity of the friendly network, ensuring that the flow of data for decision-making remains secure and uninterrupted.
Achieving Decision Dominance in a Complex World
“Directed energy, cyber capabilities, unmanned systems, and artificial intelligence are each transformative in their own right by reshaping cost curves, improving decision timelines, and expanding operational reach across every domain,” says Justin Janaskie, Chief Technology Officer. “At MAG Aerospace, we see their greatest power in convergence by integrating these capabilities into missionized, real-world operational solutions that deliver resilient ISR, precision effects, and decision dominance for our customers in the most contested and complex environments.”
The integration of these disruptive technologies is what truly unlocks decision dominance in multi-domain operations. It’s not just about having the best AI or the most advanced drones. It’s about creating a unified system where each component enhances the others.
Imagine a scenario where an unmanned aerial system detects a potential threat. Its data is instantly analyzed by an AI algorithm, which confirms the threat and identifies the target’s vulnerabilities. This information is passed to a commander, who authorizes an engagement. A cyber tool is then used to disrupt the target’s communications, while a directed-energy weapon is cued to neutralize it. This entire sequence happens in a fraction of the time it would take using conventional methods.
The Integrator’s Dilemma: Making it All Work
The disparate technologies discussed above—AI, drones, cyber, DEW—are powerful individually, but they are useless in isolation. Their value is realized only through convergence. However, bringing these systems together is a massive engineering and logistical challenge, often hindered by proprietary data formats, legacy hardware, and slow procurement cycles. This is the “Integrator’s Dilemma.”
The Role of the Lead Systems Integrator
This challenge has elevated the role of the “Lead Systems Integrator” (LSI). Companies like MAG Aerospace specialize in this “middle layer” of defense technology. They do not necessarily build the jet (the platform) or the missile (the effector); they build the “digital glue” that allows the jet to talk to the missile and the satellite to talk to the soldier.
The integrator’s task is to provide the C5ISR services—integration, operations, training, and technical services—that turn a collection of gadgets into a cohesive weapon system. This requires deep engineering expertise to reverse-engineer legacy interfaces and build “gateways” that translate data between incompatible systems. It also requires operational experience at the edge to understand how these tools are actually used in the field.
MAG’s expertise in “Turnkey C5ISR” involves taking commercial-off-the-shelf (COTS) technology and “missionizing” it for military use. This agility is essential because commercial technology (like 5G radios, AI processors, or satellite modems) often advances faster than military procurement cycles. A traditional military program might take ten years to field a new radio; by then, the technology is obsolete. By acting as a bridge between the commercial tech sector and the defense establishment, agile integrators like MAG ensure the warfighter has access to the latest capabilities on relevant timelines.
Decision Dominance through Data Fusion
The ultimate output of this integration is the Common Operational Picture (COP). In the past, a COP was a map on a wall with acetate overlays and greased pencils. Today, it is a dynamic digital twin of the battlefield, updated in real-time by thousands of sensors.
The goal is Data Fusion. AI algorithms fuse these inputs to remove duplicates and resolve ambiguities. If a satellite sees a tank at a specific coordinate and a drone hears a tank engine at the same location, the system fuses these two data points into a single “high-confidence” track. This reduces the cognitive load on the commander. Instead of staring at raw video feeds or listening to radio chatter, the commander is presented with a clear, validated picture of the battlespace. This clarity allows them to focus on the intent of the enemy rather than the location of the enemy, enabling the “Decision Dominance” that MDO seeks to achieve.
Shaping the Future of Multi-Domain Operations
This is the power of converged multi-domain operations. By leveraging cutting-edge defense technology, forces can create an information advantage that is nearly impossible for an adversary to overcome. The result is faster, better-informed decisions that lead to successful outcomes on the battlefield.
The future of defense lies in the intelligent and seamless integration of operations across all domains. The technologies driving this evolution are complex, but their goal is simple: to provide a decisive advantage through information superiority.
At MAG Aerospace, we are at the forefront of deploying the systems and expertise necessary to achieve decision dominance in Multi-Domain Operations. Our solutions in C5ISR, manned and unmanned aviation, and mission support are designed to connect the warfighter to the information they need, when they need it.
Frequent Asked Questions (FAQs)
1. What is defense technology in the context of Multi-Domain Operations?
Defense technology refers to the integrated suite of advanced tools—including Artificial Intelligence (AI), unmanned systems (drones), cyber warfare tools, and directed-energy weapons—used to achieve military objectives across the five domains of warfare: air, land, sea, space, and cyberspace. In Multi-Domain Operations (MDO), this technology is not used in isolation but is connected via a resilient network (like JADC2) to enable Decision Dominance, allowing forces to sense, decide, and act faster than the adversary.
2. How does AI impact the OODA Loop in military strategy?
Artificial Intelligence (AI) transforms the OODA Loop (Observe, Orient, Decide, Act) by automating the “Observe” and “Orient” phases.
-
- Observe: AI processes vast amounts of sensor data (satellite imagery, signals) instantly.
- Orient: Machine learning algorithms identify patterns and threats that humans might miss, creating a predictive operational picture.
- Impact: This compression allows commanders to skip straight to the “Decide” phase, reducing the reaction time from minutes to seconds. This concept is often referred to as the “Super-OODA Loop” or achieving Decision Dominance.
3. What are Directed-Energy Weapons (DEWs) and what are their advantages?
Directed-Energy Weapons (DEWs) use focused energy, such as lasers or high-power microwaves, to disable targets. They offer three primary advantages over traditional kinetic weapons (like missiles):
-
- Speed: Effects travel at the speed of light, making them ideal for intercepting fast-moving threats like hypersonic missiles.
- Cost: The “cost per shot” is negligible (often less than $10 for electricity) compared to millions for an interceptor missile.
- Depth: They have an effectively unlimited magazine as long as a power source is available, making them highly effective against drone swarms.
4. What is the difference between “Information Superiority” and “Decision Dominance”?
While related, these terms represent an evolution in military doctrine:
-
- Information Superiority is the state of possessing more or better information than the adversary. It was the goal of the 1990s and 2000s.
- Decision Dominance is the ability to act on that information faster and more effectively than the enemy. It acknowledges that having data is not enough; one must have the cognitive and technical capacity to process it and make high-quality decisions under pressure. It is the primary goal of modern Multi-Domain Operations.
5. What is the role of companies like MAG Aerospace in defense technology?
MAG Aerospace acts as a Lead Systems Integrator and provider of C5ISR (Command, Control, Computers, Communications, Cyber, Intelligence, Surveillance, and Reconnaissance) services. Their role is to:
-
- Bridge the Gap: Connect commercial technology innovation with military requirements.
- Integrate: Ensure that disparate systems (e.g., a radar from one vendor and a radio from another) work together seamlessly on a platform.
- Operate: Provide turnkey aerial ISR services, deploying manned and unmanned aircraft to gather intelligence in austere environments.
- Enable: Facilitate the Joint All-Domain Command and Control (JADC2) vision by building the resilient networks that connect the force.
6. What are the key disruptive technologies shaping the future of defense?
The four pillars of disruptive defense technology are:
-
- Artificial Intelligence & Machine Learning: For predictive analytics, autonomous navigation, and target recognition.
- Unmanned & Autonomous Systems: From “loyal wingman” drones to high-altitude ISR platforms like ATHENA-R.
- Cyber & Electromagnetic Spectrum (EMS) Tools: For electronic warfare, jamming, and network defense.
- Directed Energy: High-energy lasers and microwaves for cost-effective air and missile defense.
7. Why is “Integration” critical in modern defense strategies?
Integration is critical because modern threats are too complex for any single platform to handle. A fighter jet cannot win a war alone; it needs data from space, cyber protection for its networks, and logistical support from the ground. Integration ensures that data flows across these multi-domain boundaries. Without effective integration, advanced technologies become “silos of excellence”—capable individually but failing as a system. The ability to integrate hardware and software to form a “kill web” is the defining characteristic of a modern, ready force.
8. How does “Predictive Logistics” enhance military readiness?
Predictive Logistics uses AI and sensors to monitor the health of equipment in real-time. Instead of waiting for a part to break (reactive maintenance) or replacing it on a fixed schedule (preventive maintenance), AI predicts exactly when a component will fail. This allows for:
-
- Precision Sustainment: Shipping only the necessary parts to the front lines, reducing the logistical tail.
- Increased Readiness: Preventing unexpected breakdowns during combat operations.
- Cost Savings: Avoiding unnecessary maintenance cycles.
9. What is the “Transport Layer” in C5ISR?
The Transport Layer is the communications infrastructure that moves data between sensors, shooters, and commanders. It includes:
-
- Satellite Links (SATCOM): For global, long-range connectivity.
- Tactical Radios: For line-of-sight communication between ground units.
- 5G Networks: For high-speed, low-latency data transfer at the edge.
- Free-Space Optics: Using lasers for secure, jam-resistant links. Defending the transport layer from electronic jamming is crucial for maintaining the Common Operational Picture.
Explore how our capabilities are shaping the future of multi-domain operations.

