- Signals Intelligence (SIGINT) Modernization: The transition from legacy collection methods to advanced, high-altitude Deep Sensing platforms is redefining the intelligence landscape. The global SIGINT market, driven by these upgrades, is projected to surge from approximately $18.5 billion in 2025 to nearly $30 billion by 2035.
- Agentic AI and Cognitive SIGINT: Artificial intelligence has transitioned from a generative assistant to an autonomous decision engine. Agentic AI is now foundational to the SIGINT Processing, Exploitation, and Dissemination (PED) cycle, automating target recognition, classifying electromagnetic signals at the edge, and dramatically reducing sensor-to-shooter timelines.
- Electronic Warfare and Cyber Convergence: The modern battlespace demands “Spectral Dominance.” SIGINT, Cyber Operations (CO), and Electronic Warfare (EW) are entirely converged, utilizing AI-driven cyber-physical attacks and software-defined dynamic frequency hopping to neutralize peer adversaries.
What Is Signals Intelligence (SIGINT)?
Signals Intelligence is the name given to the collection of signals and communication-related information that is used to gain insight into the workings of an adversary or target. SIGINT uses various methods, such as:
- Listening to radio waves
- Monitoring satellite communications
- Decoding encrypted messages
- Intercepting telephone conversations
- Analyzing open-source data
To obtain this kind of information, intelligence agencies may employ electronic means, including satellites, aircraft with special equipment, bugging devices, and interception of fiber optic cables. All data collected through SIGINT can be used for counterintelligence purposes by determining the capabilities and intentions of a foreign power or other adversaries.
The Evolution and Strategic Imperative of Signals Intelligence
Signals Intelligence, universally recognized by the acronym SIGINT, is the specialized intelligence-gathering discipline fundamentally predicated on the interception, collection, and analysis of electronic signals, radar emissions, and communications. For over a century, it has remained one of the most vital and closely guarded instruments utilized by military organizations and national intelligence apparatuses to ascertain the capabilities, activities, and strategic intentions of foreign adversaries. While the National Security Agency (NSA) functions as the premier and most heavily funded SIGINT authority within the United States, parallel capabilities are embedded deeply across the intelligence community, including the CIA’s Directorate of Digital Innovation and the FBI’s National Security Branch.
The genesis of SIGINT traces back to the early 1900s, coinciding with the advent of secure, encoded radio transmissions during the First and Second World Wars. In these early conflicts, the strategic importance of intercepting radio coordination became glaringly apparent, leading to the establishment of dedicated radio interception units. Throughout the Cold War, the United States and the Soviet Union invested massive national resources into creating complex SIGINT architectures, culminating in powerful global infrastructures that included satellite telemetry monitoring, undersea cable interception, and over-the-horizon radar networks. Information gathered using these SIGINT methods consistently aided in quicker, more effective decision-making and the identification of existential threats.
In the post-Cold War era, and particularly during the two decades of the Global War on Terror, SIGINT systems were largely optimized for counterinsurgency (COIN) operations. These operations took place in relatively uncontested airspace where slow-moving aircraft could loiter for hours, hoovering up cellular and radio communications from localized insurgent networks.
However, the strategic and geopolitical realities of 2026 demand an entirely different operational architecture. The resurgence of near-peer adversaries—specifically the People’s Republic of China and the Russian Federation—has forcibly shifted military focus away from asymmetric conflicts and toward Large-Scale Combat Operations (LSCO) and Multi-Domain Operations (MDO). These near-peer competitors have spent the last two decades constructing formidable Anti-Access/Area Denial (A2/AD) networks comprising integrated air defense systems (IADS), long-range precision surface-to-air missiles, and advanced electromagnetic jamming complexes. Consequently, modern SIGINT must operate at significantly extended standoff distances, penetrating the “electronic shield” of adversaries while maintaining absolute stealth and resilience across a highly congested electromagnetic spectrum.

Types of SIGINT
To comprehend the modernization of this domain and the technological requirements of 2026, one must first delineate the three distinct, yet deeply interconnected, sub-disciplines of SIGINT.
Signals Intelligence can be broken down into three types:
- Communications Intelligence (COMINT)
- Electronic Intelligence (ELINT)
- Foreign Instrumentation Signals Intelligence (FISINT)
They can all work in combination or as individual entities. Let’s explore them a little further.
1. Communications Intelligence (COMINT)
COMINT, or Communications Intelligence, is an intelligence-gathering activity that focuses on intercepting and analyzing communications between people or groups to gain insight into the activities of foreign powers and other adversaries. Collection techniques include:
- Conducting surveillance of wireless transmissions
- Decoding encrypted messages
- Monitoring telephone conversations
- Open-source data
The collection techniques are vast, ranging from the surveillance of simple wireless radio transmissions and telephone monitoring to the highly complex decoding of encrypted digital messages and the analysis of vast open-source data repositories. By intercepting these communications, intelligence agencies gain direct access to the operational planning and diplomatic intentions of foreign powers.
In 2026, the landscape of COMINT has been irreversibly altered by the ubiquitous proliferation of end-to-end encryption on both commercial and military-grade platforms. This cryptographic hardening has drastically reduced traditional, easily exploitable COMINT yields. In response, intelligence agencies have been forced to pivot their methodologies, increasingly relying on offensive cyber intrusions, metadata pattern-of-life analysis, and advanced technical exploitation to bypass encryption at the endpoint before the data is scrambled.
By intercepting communications through COMINT, intelligence agencies can gain access to valuable information that can help them in their mission.
2. Electronic Intelligence (ELINT)
Another subset of SIGINT is called Electronic Intelligence or ELINT. This type of signals intelligence gathering focuses on collecting and analyzing non-communication emissions from various electronic systems.
This includes varying forms of radar, radio frequency receiver systems, telemetry devices, sensors, and satellite beacon systems.
In a modern battlespace dictated by A2/AD systems, ELINT is arguably the most critical component for immediate tactical survival. It involves detecting, identifying, geolocating, and characterizing hostile radar systems, radio frequency receiver systems, telemetry devices, and satellite beacon systems. By meticulously analyzing the pulse repetition frequencies, scan rates, and power outputs of adversary radars, ELINT platforms provide the foundational data necessary to establish the Electronic Order of Battle (EOB). This data allows ground commanders to map the exact locations of surface-to-air missile (SAM) sites and early warning radars, thereby defining the safe corridors and lethal engagement zones for friendly aviation and ground maneuver forces. The rising military demand for these advanced detection capabilities in increasingly complex electronic warfare environments makes ELINT the largest revenue-generating segment within the SIGINT market.
3. Foreign Instrumentation Signals Intelligence (FISINT)
FISINT, or Foreign Instrumentation Signals Intelligence, is an intelligence-gathering discipline that focuses on collecting and analyzing data from foreign sources. FISINT primarily uses non-communications signals and can include:
- Radar mapping
- Tracking of air and sea vessels
- Satellite imagery analysis
- Nuclear detection
- Missile guidance system exploitation
FISINT is the highly specialized interception of non-communication telemetry data, video data links, and tracking signals emitted during the testing and operational deployment of foreign aerospace, surface, and subsurface systems. This discipline includes radar mapping, tracking of air and sea vessels, nuclear detection, and the exploitation of missile guidance systems. FISINT plays a vital corroborating role in broader surveillance operations. As nations aggressively test hypersonic glide vehicles, autonomous drone swarms, and sixth-generation fighter components in 2026, FISINT provides unparalleled insights into the technical parameters, flight envelopes, and maximum capabilities of adversary weapons systems long before they are ever fielded in active combat.
The Artificial Intelligence Paradigm Shift: From Generative to Agentic AI
As the hardware platforms evolve to fly higher and look deeper, the volume of data they collect has expanded exponentially. The sheer density of signals traversing the electromagnetic spectrum in 2026—exacerbated by widespread 5G cellular networks, automated battlefield Internet of Things (IoT) devices, and dense urban environments—has created a “data deluge”. In the contemporary intelligence environment, the defining constraint is no longer a scarcity of information, but rather an overabundance of it; human attention and cognitive bandwidth have become the ultimate limiting factors.
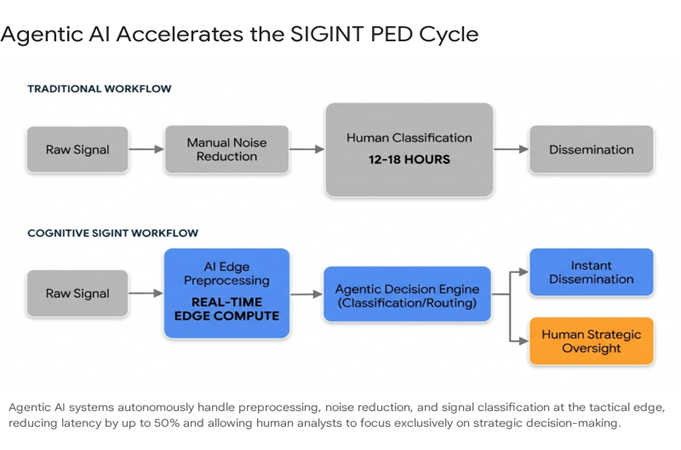
Historically, the SIGINT Processing, Exploitation, and Dissemination (PED) cycle was highly manual and painstakingly slow. It often required 12 to 18 person-hours for analysts to manually sift through noise, isolate a single Signal of Interest (SOI), and classify the threat. In a fast-paced Multi-Domain Operation where hypersonic missiles cross theaters in minutes, a 12-hour processing delay is functionally useless. Consequently, Artificial Intelligence (AI) and Machine Learning (ML) rapidly evolved from experimental research tools into mandatory operational requirements, giving rise to the discipline of “Cognitive SIGINT”.
In 2026, the global technology landscape is experiencing a massive paradigm shift from assistive or generative AI toward Agentic AI. For the past few years, the focus was on Generative AI—large language models that respond to prompts, summarize texts, or generate code based on historical training data. While useful for drafting reports, these models are essentially “read-only” assistants.
Agentic AI, however, represents the transition of artificial intelligence into an autonomous decision engine. Agentic systems are proactive, goal-oriented entities capable of reasoning, planning, executing multi-step workflows, autonomously querying databases, taking actions, and adapting to real-time environmental changes with minimal human oversight. As industry experts note, 2026 is the year AI evolves from an instrument into a partner, moving out of experimentation and becoming the core operating fabric of enterprise and military automation.
Cognitive SIGINT and the Autonomous PED Cycle
Within the SIGINT and Electronic Warfare domains, Agentic AI is fundamentally revolutionizing the PED cycle and reducing sensor-to-shooter timelines.
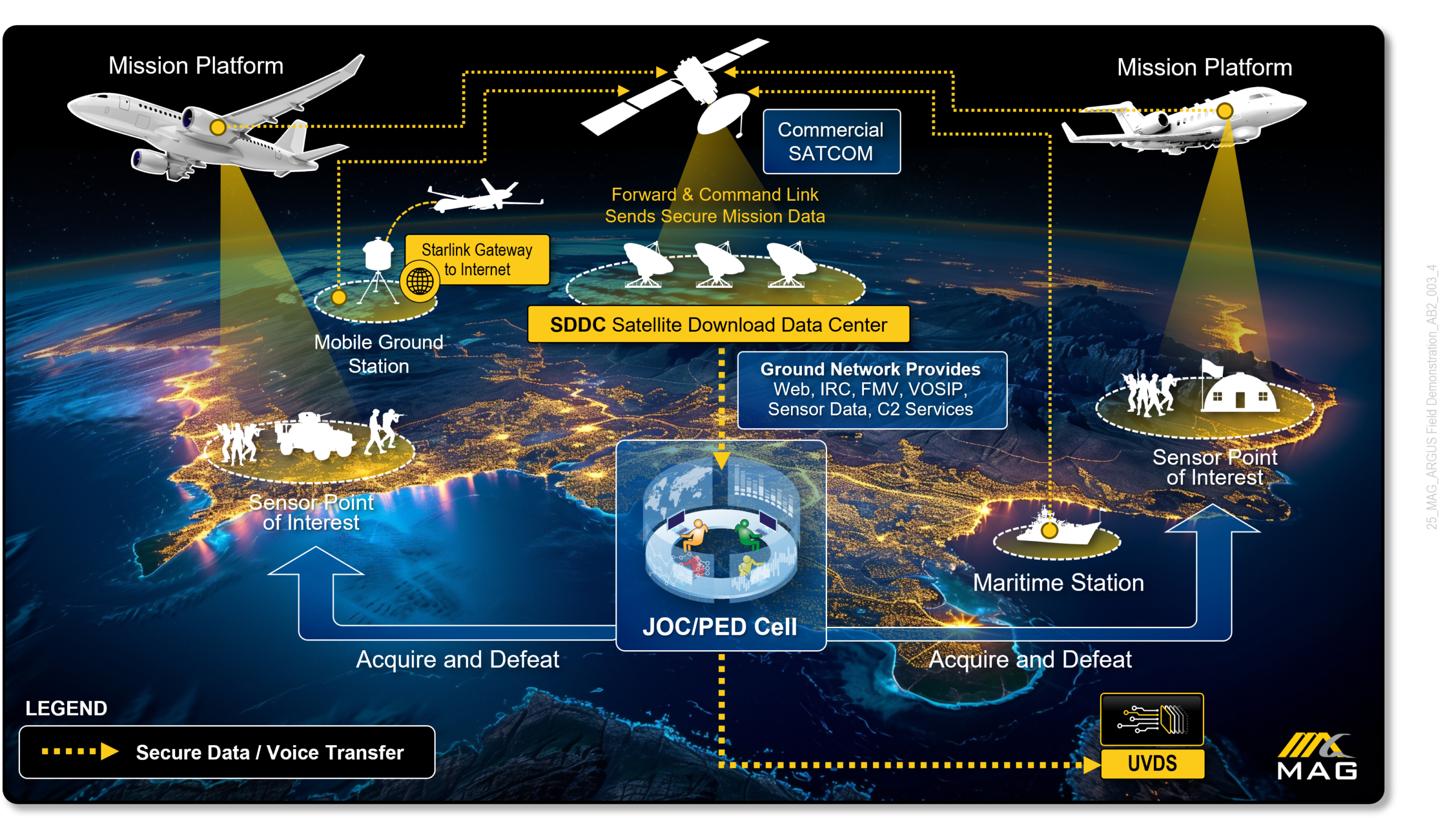
Instead of routing terabytes of raw radio frequency (RF) data back to a centralized server farm—which consumes massive bandwidth and introduces fatal latency—modern platforms utilize Edge AI. AI agents are deployed directly onto platforms like the HADES jet or terrestrial TLS systems. These embedded models execute streaming analytics in real-time at the point of collection.
The process begins with AI-driven automation handling the tedious preprocessing of raw data. Machine learning algorithms autonomously perform noise reduction, filter out known civilian frequencies, detect anomalous signals, and extract key features, eliminating vast swaths of irrelevant data before it ever reaches high-power processing elements like general-purpose graphics processing units (GPGPUs).
Once a signal is isolated, Cognitive SIGINT utilizes deep neural networks to instantly classify and identify the emission. Previously, if an adversary deployed a novel radar signal in theater, forces had to record the signal, send it back to a lab, and wait for months for engineers to develop a purpose-built hardware countermeasure. Today, cognitive systems learn from the environment dynamically. They analyze the unknown signal’s parameters, classify the threat, and autonomously reconfigure the platform’s software-defined radios and electronic support measures to instantly jam or exploit the signal.
By automating these complex adaptive workflows, Agentic AI systems process data two to three times faster than manual methods, reduce latency by up to 50%, consume 20% to 30% less power, and accurately prioritize intercepted signals based on strategic urgency. This creates an “augmented intelligence” environment. The AI acts as a “silicon-based workforce,” handling the overwhelming data triage and workflow orchestration, allowing human SIGINT professionals to escape the noise and focus exclusively on higher-level strategic analysis, exception management, and decision support.
Navigating High-Trust Exploitation and Cyber-SIGINT
The convergence of cyber operations and SIGINT means that AI is not solely a defensive or analytical tool; it is aggressively weaponized by threat actors. Cybersecurity threat intelligence reports for 2026 indicate a fundamental evolution in adversary tactics, shifting away from complex, expensive, and bespoke zero-day exploits. Instead, the modern adversary operates on an industrialized scale driven by a cold “Measure of Effectiveness” (MOE) metric—a calculation optimizing the ratio of effort to operational outcome.
AI allows threat actors to automate the discovery of connective tissue linking sensitive data. Attackers now prioritize “high-trust exploitation,” utilizing AI to steal session tokens, mimic legitimate user behavior, and hijack trusted internal tools (such as corporate repositories or calendars) to bypass perimeter defenses entirely. Because these threat actors integrate intelligence and technology into a single continuous system to achieve throughput, defensive cyber-SIGINT requires equally autonomous countermeasures. Organizations are heavily investing in AI-driven Zero Trust Architectures (ZTA), continuous authorization (cATO) protocols, and machine learning models capable of scanning vast internal network signals to detect anomalous behavioral patterns in milliseconds, effectively halting lateral movement before data exfiltration occurs.
Defense Policy and the AI-First Industrial Base
The integration of Agentic AI and Cognitive SIGINT is heavily mandated and supported at the highest levels of government. In early 2026, the U.S. Department of War issued a series of coordinated memoranda establishing a U.S. “AI-first” wartime-speed agenda for data and innovation. The strategy designates core innovation organizations and aims to achieve “America’s Military AI Dominance”.
A central pillar of this agenda is the transformation of defense data systems (like Advana) into a unified War Data Platform (WDP) to standardize data access specifically for the deployment of “agentic AI” across the enterprise. The strategy identifies several “Pace-Setting Projects,” forcing the defense industrial base to rapidly develop playbooks for AI agent deployment.
This aggressive acceleration has not been without friction. The integration of commercial AI into military applications has sparked intense ethical and supply chain debates. Notably, a public dispute erupted in early 2026 when the Pentagon designated the prominent AI firm Anthropic as a “supply chain risk” following failed negotiations. Anthropic refused to grant the military exceptions to use their Claude AI model for domestic mass surveillance or fully autonomous weapons systems. In response, the administration ordered federal agencies and defense contractors to phase out Anthropic technology, highlighting the complex, high-stakes intersection of commercial AI ethics and national security imperatives.
Ultimately, maintaining technological superiority in SIGINT requires leveraging the entire commercial sector. Through flexible procurement mechanisms like Other Transaction Authority (OTA) and the Software Fast Track (SWIFT) initiatives, the defense industry is bypassing traditional bureaucratic bottlenecks to integrate cutting-edge algorithms and software-defined radios at the speed of relevance.
Military Importance of Signals Intelligence
This intelligence use by military personnel plays a crucial role in providing a better understanding of their adversary’s plans and capabilities. SIGINT is often combined with other forms of intelligence, such as HUMINT (Human Intelligence) which gathers information from human sources.
The primary purpose of SIGINT is to collect tactical information that the military can use against its adversaries before they can act. It also helps the military analyze incoming data quickly to make decisions more efficiently. This can be especially important in times of war, where every second counts.
SIGINT has changed drastically over the years thanks to technological advancements that have allowed for more sophisticated methods of gathering information. It now includes things like electronic warfare, counter-surveillance, and cyber operations that are all being used by modern militaries for their own purposes.
SIGINT has become an invaluable tool for militaries worldwide, giving them a much greater opportunity to stay ahead of their enemies and anticipate potential threats before they become a reality.
It’s no secret that SIGINT is a powerful tool that can be used to gain an advantage over adversaries. It has become increasingly important in modern warfare and is now being used for more sophisticated operations such as electronic warfare, counter-surveillance, and cyber operations.
With the help of SIGINT, militaries worldwide have access to valuable information about their enemies, which helps them make better decisions faster. As technology continues to advance, so does the use of SIGINT in military operations, and it will remain an invaluable asset for years to come.
The exponential proliferation of electromagnetic signals mandates that human cognitive capacity be augmented by a robust silicon-based workforce. The integration of Agentic AI at the tactical edge—filtering noise, executing autonomous classifications, and dynamically adapting to novel electronic threats—has fundamentally transformed the Intelligence Processing, Exploitation, and Dissemination cycle. Organizations, intelligence agencies, and defense contractors that successfully harmonize modular open systems architectures with these autonomous intelligence agents will secure the ultimate strategic advantage: spectrum dominance and decision superiority at the speed of the modern battlespace.
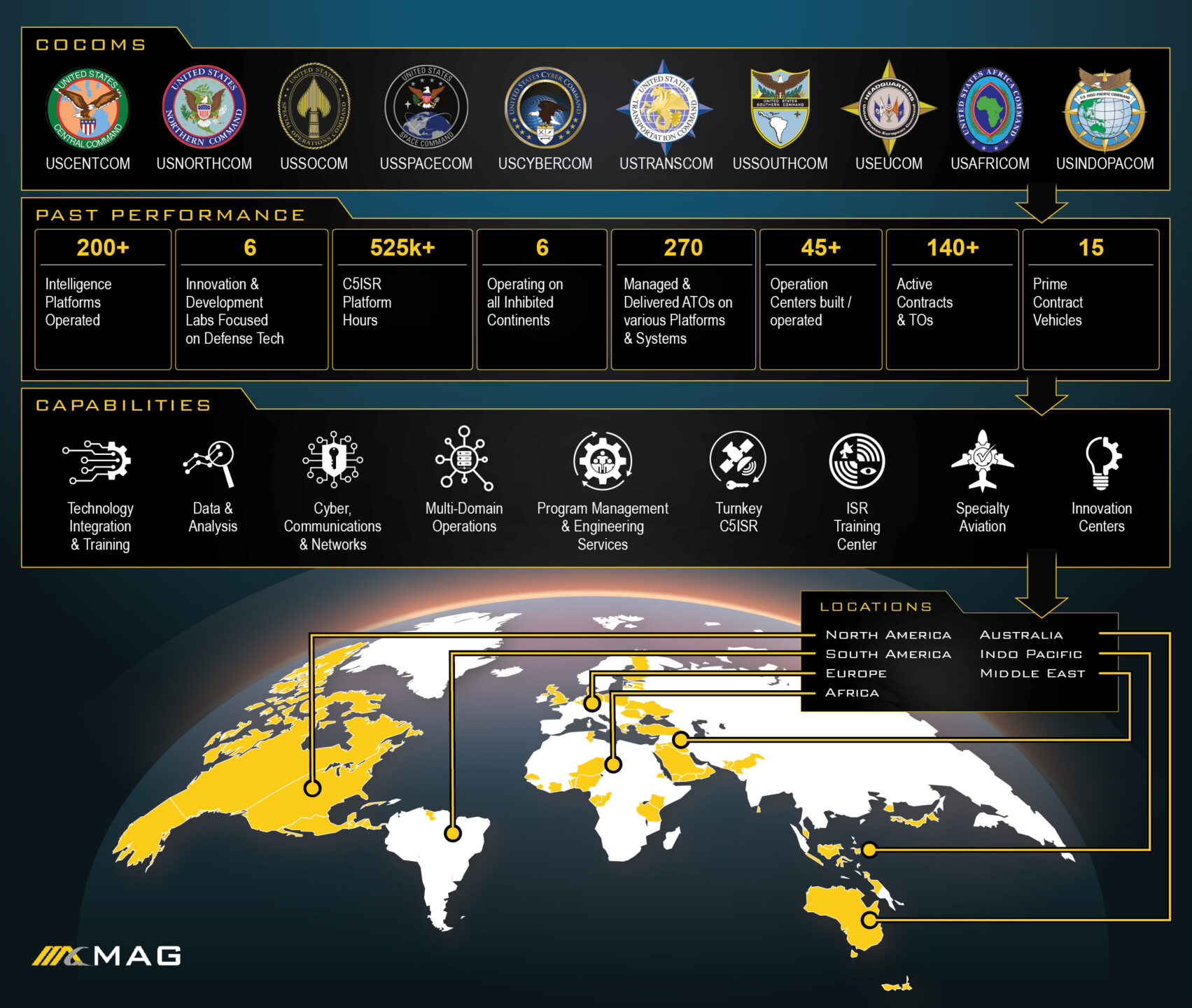
Discover the Benefits of MAG Training Facilities
At our Intelligence, Surveillance, Reconnaissance Training Facility (ISRTC) in Moore County, North Carolina, MAG plays a major role integral to today’s mission in developing and deploying SIGINT technologies. The ISRTC plays an integral role in today’s mission by identifying new collection methods, integrating them into existing systems, and providing comprehensive training and support to government partners, empowering them to utilize SIGINT technology effectively. By doing so, we can provide our partners and customers with the best possible capabilities.

At MAG, we draw upon our extensive knowledge base to offer training and support to our partners and customers, empowering them to use SIGINT technology effectively and achieve their mission goals. To ensure that we remain at the forefront of our field, we stay up-to-date with the latest technological advancements and strive to understand the needs of our partners and customers, demonstrating our unwavering commitment to the mission.
In today’s threat environment, there is an increased focus on the near-peer threats facing our nation. This shift in priorities has driven the Army and other service branches to pursue efforts aimed at optimizing SIGINT sensors within both airborne- and ground-based intelligence programs to combat emerging threats. This includes implementing new or enhanced SIGINT sensors capable of collecting on advanced communications and weapons systems.
Other efforts include enabling cooperative tasking, collection, and geolocation amongst airborne, space, and ground systems. These efforts will ensure platforms and sensors are more effective and resilient against a near-peer adversary in a degraded or contested environment and in the multi-domain operations (MDO) fight.
Frequently Asked Questions (FAQ)
1. What is Signals Intelligence (SIGINT) and how is it utilized in modern warfare? Signals Intelligence (SIGINT) is the highly specialized intelligence-gathering discipline involving the collection, interception, and rigorous analysis of electronic signals. It is primarily divided into Communications Intelligence (COMINT) for intercepting human or text-based communications, Electronic Intelligence (ELINT) for analyzing non-communication emissions like surface-to-air missile radar systems, and Foreign Instrumentation Signals Intelligence (FISINT) for capturing telemetry from adversary weapons testing. In modern warfare, SIGINT is crucial for mapping the Electronic Order of Battle and protecting friendly forces from advanced air defenses.
2. How does Agentic AI differ from Generative AI, and how is it changing Cognitive SIGINT? While Generative AI focuses on producing text or code based on historical training data as a “read-only” assistant, Agentic AI acts as a proactive, autonomous decision engine capable of planning and executing complex, multi-step workflows. In the realm of Cognitive SIGINT, Agentic AI operates directly at the tactical edge to autonomously preprocess raw radio frequency data, classify novel radar signals using deep neural networks, and cross-cue electronic warfare systems in real-time. This automates the PED cycle, reducing manual processing times by up to 50% and enabling instantaneous threat response.
3. What are Multi-Domain Operations (MDO) and why is Deep Sensing critical to them? Multi-Domain Operations (MDO) is the military doctrine that synchronizes offensive and defensive capabilities across land, air, sea, space, and cyberspace to defeat highly sophisticated near-peer adversaries. Deep sensing is a critical, foundational component of MDO; it involves using high-altitude platforms, space-based assets, and advanced sensors to collect intelligence, geolocate targets, and provide early warnings from deep within hostile, contested territory, far beyond the traditional line of sight.
4. What role does the defense industrial base, such as MAG Aerospace, play in airborne ISR modernization? Defense contractors act as the vital lead systems integrators for highly complex military programs. Companies like MAG Aerospace serve as prime contractors on massive sustainment and integration projects like the STORM program out of Aberdeen Proving Ground, and partner with firms like L3Harris on bridging strategies like the ATHENA-R jet program. These companies manage the turnkey lifecycle of C5ISR systems, operating advanced training facilities like the ISRTC in Moore County, NC, to ensure that commercial-off-the-shelf technologies and open systems architectures are rapidly and safely fielded to the military.
5. What does “Spectral Dominance” mean in the context of Electronic Warfare? Spectral Dominance refers to achieving total control over the electromagnetic spectrum (EMS). In 2026, cyberspace operations, SIGINT, and Electronic Warfare have converged. To achieve Spectral Dominance, militaries use software-defined systems to passively detect enemy emissions, actively jam adversary communications using dynamic frequency hopping, and utilize low-signature, disposable radios to hide their own communications within the civilian noise floor, effectively neutralizing the enemy’s ability to coordinate while preserving friendly data links.
With years of experience developing and deploying advanced systems that enable intelligence gathering and analysis, MAG is the perfect partner for any organization looking to lead the pack. Contact MAG today to learn how they can help you stay ahead of the curve with their cutting-edge technology and solutions that exceed expectations.
Updated March 2026