By Robert Connell, MAG’s Vice President of Enterprise Growth (Colonel (Ret.) U.S Army 7th Special Forces Group (Airborne)
The Impact of AI on Defense Capabilities in 2026:
- Global Market Expansion: The global Command, Control, Computers, Communications, Cyber, Intelligence, Surveillance, and Reconnaissance (C5ISR) market was valued at $144.23 billion in 2024 and is projected to reach $189.00 billion by 2030, expanding at a Compound Annual Growth Rate (CAGR) of 4.7%.
- AI Defense Spending Surge: The specialized Artificial Intelligence in Defense market is experiencing dramatic acceleration, valued at $9.13 billion in 2025 and forecast to reach $29.48 billion by 2035, representing a 12.48% CAGR.
- Operational AI Adoption Rates: By the conclusion of 2025, 89% of global defense forces had actively deployed artificial intelligence across intelligence, surveillance, reconnaissance (ISR), autonomous systems, and cyber operations.
- Decision-Making Acceleration: Military operators utilizing AI-augmented decision support tools complete 12% more operational tasks and execute complex workflows 25% faster than baseline human performance metrics without AI assistance.
- Cyber Threat Mitigation: AI-enabled predictive analytics and continuous network monitoring have drastically reduced the average dwell time of malicious actors within defense networks, plummeting from an average of 243 days in 2012 to merely 11 days by 2024.
- Software and Hardware Dynamics: While traditional hardware components accounted for the largest market share in 2024 (over 43%), specialized AI software designed for autonomous capabilities and decision tools is the fastest-growing sector, projected to grow at an 11.74% CAGR through 2031.
What is C5ISR and Why Does It Require Artificial Intelligence?
C5ISR stands for Command, Control, Computers, Communications, Cyber, Intelligence, Surveillance, and Reconnaissance. It represents the integrated digital and physical architecture used by military leaders to gather intelligence and direct forces. These systems require artificial intelligence because the sheer volume, velocity, and variety of data collected by modern multi-domain sensors far exceed human processing capacity. AI filters environmental noise, highlights tactical anomalies, and delivers actionable insights in real time, preventing critical intelligence from being delayed in massive data backlogs.
Modern defense operations generate unprecedented amounts of data every second. From high-altitude satellite imagery and unmanned aerial systems (UAS) to low-echelon ground-sensor feeds and open-source intelligence, combatant commanders face the immense challenge of turning raw information into actionable intelligence with speed and precision. The transition from traditional, human-reliant analytical methods to AI-augmented intelligence represents a fundamental paradigm shift in modern warfighting. Without artificial intelligence, critical intelligence frequently gets trapped in a backlog of unanalyzed full-motion video feeds, acoustic signatures, and electronic radar logs.
Artificial intelligence and machine learning (ML) technology acts as a critical force multiplier across the entire battlespace. The ultimate objective extends beyond achieving mere visibility of the battlefield; it encompasses the accurate representation of multi-domain threats, proper attribution of adversarial movements, and the rapid positioning of command centers to achieve decision superiority. As governments continuously upgrade their defense infrastructures to counter evolving peer and near-peer threats, the demand for integrated C5ISR solutions driven by 5G networks, cloud computing, and autonomous technologies dictates the future of operational effectiveness.
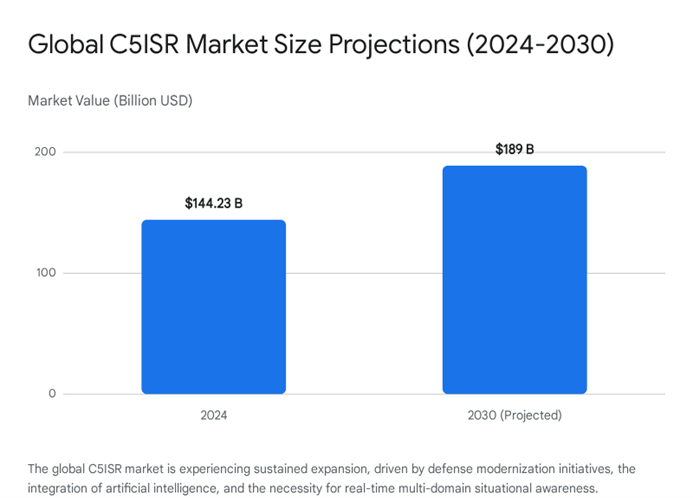
Geopolitical tensions and the rising complexity of asymmetric warfare act as primary catalysts for this technological transformation. Nations are heavily prioritizing digital transformation initiatives to establish network-centric warfare capabilities. The United States Department of Defense (DoD), for instance, has significantly increased funding allocations for advanced digital battlefield infrastructures, emphasizing the integration of commercial technology and modular open systems approaches (MOSA) to sustain information dominance.
| Market Segment | 2024-2026 Valuation Status | Projected Growth (CAGR) | Strategic Drivers |
|---|---|---|---|
| Global C5ISR Market | $144.23 Billion (2024) | 4.7% (2025-2030) | Defense modernization, multi-domain operations, real-time situational awareness needs. |
| Defense AI Market | $9.13 Billion (2025) | 12.48% (2026-2035) | Asymmetric warfare threats, autonomous platform integration, predictive logistics. |
| C5ISR Hardware | 43.10% Market Share (2025) | Stable Core Growth | Continued procurement of sensors, edge processing units, and communication relays. |
| C5ISR Software | Accelerating Adoption | 11.74% (2026-2031) | AI-enabled decision tools, generative engine optimization for data retrieval, automated target recognition. |
| Airborne End-Use | Over 35% Market Share (2024) | Highest Sector Growth | Rising UAV adoption, sixth-generation fighter roadmaps, high-altitude ISR platforms. |
How Does Edge Computing Enable Real-Time Sensor Fusion?
What is the role of edge computing in military sensor fusion and C5ISR applications? Edge computing allows raw sensor data to be processed locally at the source of collection—such as directly onboard a surveillance drone, naval vessel, or tactical ground vehicle—rather than transmitting it to a centralized cloud server. This drastically reduces latency, conserves critical bandwidth, and ensures that multi-modal sensors can continuously fuse data and generate insights even in highly contested environments where communications are jammed or degraded.
In high-stakes combat environments, the latency introduced by waiting for data to travel from a battlefield sensor to a centralized command data center and back can cost lives. Edge computing completely resolves this architectural bottleneck. By relocating the computational power to the extreme tactical edge, military assets can act autonomously and instantly. When edge computing architectures are combined with advanced machine learning models, sensors on unmanned aerial vehicles or tactical ground units analyze environmental information instantaneously.
For example, a high-altitude surveillance drone processing its own live video feed can utilize onboard computer vision to identify a specific hostile vehicle classification, extract the precise geolocation, and transmit only those relevant coordinates back to the command center. This edge-processing methodology dramatically reduces the bandwidth required for transmission and provides combatant commanders with immediate, uncluttered situational awareness.
The Mechanics of Multi-Modal Sensor Fusion
The true power of edge computing is realized through multi-modal sensor fusion. Modern military platforms are equipped with a diverse array of sensors, including electro-optical (visual), infrared (thermal), acoustic, and radio frequency (RF) receivers. In legacy C5ISR paradigms, these distinct data streams were often transmitted to separate terminals and analyzed in silos by different human operators, creating a fragmented view of the battlefield.
AI-enabled edge computing fuses these disparate inputs into a single, cohesive Common Operating Picture (COP). By executing complex sensor, data, and information fusion algorithms directly on ruggedized, power-conscious edge devices, defense systems mitigate the stringent Size, Weight, and Power (SWaP) constraints that have historically limited autonomous operations. This collaborative computing approach supports decentralized information sharing, allowing multiple edge nodes (such as a swarm of drones) to communicate findings and corroborate target identities without relying on a central server.
| Edge Computing Capability | Traditional Cloud Architecture | AI-Enabled Tactical Edge Architecture | Tactical Advantage Gained |
|---|---|---|---|
| Data Processing Location | Centralized distant servers; requires full data transmission. | Localized on the sensor platform (UAV, ground vehicle). | Zero-latency analytics; immediate tactical insight. |
| Bandwidth Consumption | Extremely high; requires continuous streaming of raw full-motion video. | Minimal; transmits only actionable metadata and coordinates. | Preserves spectrum for critical command communications. |
| Sensor Fusion Integration | Siloed analysis requiring human synthesis. | Automated multi-modal fusion (Visual, IR, RF). | Creates an instant, holistic Common Operating Picture. |
| Operational Resiliency | Vulnerable to network jamming and disconnection. | Fully autonomous operation during communications blackout. | Ensures continuous intelligence gathering in A2/AD zones. |
Resiliency in Contested Electromagnetic Environments
A defining characteristic of warfare in 2026 is the prevalence of highly contested electromagnetic spectrums. Peer adversaries routinely utilize advanced electronic warfare (EW) jamming and GPS-spoofing techniques to disrupt allied communications and navigation. Edge-enabled AI military systems maintain full functionality when networks face such severe disruptions.
If an adversarial attack severs the connection to the broader network, edge devices continue to gather, fuse, and analyze data autonomously. The AI algorithms prioritize the gathered intelligence based on threat severity. Once the secure connection is re-established, the system instantly updates the network with its prioritized findings, ensuring that no critical intelligence is missed during the blackout. This resilience ensures that forces maintain continuous situational awareness, a core requirement for executing multi-domain operations against sophisticated near-peer threats.
Furthermore, the integration of conversational AI interfaces—powered by open-source large language models (LLMs) like Llama or Mistral—at the tactical edge is transforming human-machine interaction. Instead of manually parsing through raw telemetry or complex graphical user interfaces, a field operator can query the edge system using natural language. The AI synthesizes the fused sensor data and provides a direct, concise answer summarizing the threat posture, significantly streamlining the cognitive workload during high-stress combat operations.
How Does Artificial Intelligence Compress the Military OODA Loop?
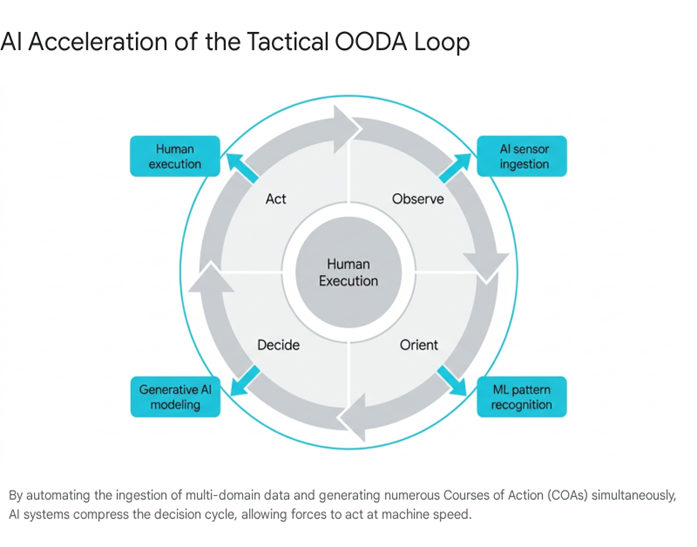
The OODA Loop—Observe, Orient, Decide, Act—is a foundational military framework for combat decision-making. AI drastically compresses this cycle by automating data collection (Observe), utilizing machine learning for instantaneous pattern recognition (Orient), and generating predictive multi-variable courses of action (Decide). This technological acceleration allows military forces to operate at machine speed, outpacing human cognitive limits and reacting faster than adversaries.
Developed by military strategist and U.S. Air Force Colonel John Boyd, the OODA loop posits that the combatant who successfully cycles through the decision-making process faster and more accurately than their opponent will dictate the flow of the engagement and ultimately achieve victory. In historical conflicts, progressing through each phase of this loop could take hours, days, or even weeks. Today, the integration of artificial intelligence is compressing this cycle to mere minutes or milliseconds, fundamentally altering the tempo of modern warfare.
Observation and Orientation at Machine Speed
In the “Observe” and “Orient” phases, human limitations present significant bottlenecks. Human operators can only monitor a finite number of screens and process a limited amount of information simultaneously. AI algorithms, however, excel by continuously ingesting massive datasets from interconnected satellite constellations, unmanned drones, air defense arrays, and electronic warfare platforms.
Where a human intelligence staff might require hours to orient themselves to a rapidly shifting battlefield, AI models analyze historical operational data, real-time weather patterns, troop movements, and logistical supply lines instantaneously to build accurate, predictive mental models of the environment. AI establishes a baseline of normal behavior across the battlespace and immediately highlights deviations, effectively automating the orientation process and presenting commanders with a pre-synthesized, highly accurate view of the operational theater.
Decision Support and the Human-Machine Continuum
The most profound impact of AI occurs within the “Decide” phase. In complex combat operations, commanders must evaluate dozens of dynamic variables simultaneously. Historically, due to severe time constraints, a human commander and their staff could typically formulate and evaluate only two or three potential Courses of Action (COA).
Modern generative AI systems and agentic workflows obliterate this limitation. A system like COA-GPT can generate dozens of alternative, highly detailed COAs from the same initial battlefield configuration. The AI systematically varies maneuver structures, axes of effort, tactical risk profiles, and resource allocations. For example, automated resource allocation algorithms can instantaneously determine the safest and fastest route for a supply convoy, continuously and automatically adjusting the path if a new kinetic or cyber threat is detected ahead.
It is a critical tenet of modern military doctrine that these systems are designed to augment human leaders, not fully replace them in lethal targeting or strategic command. The AI handles the heavy mathematical lifting, the complex multi-variable modeling, and the rapid generation of options. It then presents operators with optimized recommendations. This dynamic creates a blurred human-machine decision-making continuum, where the raw processing speed of the machine complements the ethical judgment, operational experience, and contextual intuition of the human commander. Empirical data underscores the efficacy of this approach: when operators are properly trained to interface with AI augmentation, task completion rates increase by 12%, and overall operational execution speed increases by 25% compared to non-augmented baseline metrics.
Managing Risks in High-Speed Warfare Environments
The relentless pursuit of operational speed is not without significant strategic risk. Conceptualizing AI implementation solely through the lens of accelerating the OODA loop can mask the immense complexities and potential pitfalls of human-machine teaming. If the handoff between machine synthesis (prediction) and human judgment (decision) becomes incongruous or misaligned, unintended strategic consequences rapidly arise.
In a highly networked battlespace, a single false signal, an adversarial data poisoning attack, or a generative AI hallucination can acquire strategic significance if acted upon too quickly without sufficient human comprehension. An over-reliance on algorithmic outputs without the requisite critical thinking can lead to systemic failures when unprecedented scenarios arise that fall outside the AI’s training data. Therefore, rigorous developmental testing, the establishment of clear AI explainability metrics, and comprehensive workforce development training are essential prerequisites to ensure trust, transparency, and resilience in AI-enabled C5ISR platforms.
How Are Machine Learning and Autonomous Systems Advancing Threat Detection?
How is machine learning utilized for automated threat detection and predictive maintenance in defense operations? Machine learning algorithms are trained on vast datasets to recognize complex acoustic, visual, and electronic patterns, enabling them to identify subtle battlefield threats that human operators often overlook. Beyond external threat detection, ML powers predictive maintenance by continuously monitoring internal equipment telemetry to detect anomalies and forecast mechanical failures before they occur, optimizing overall asset readiness.
Automated Target Recognition (ATR)
Traditional radar, sonar, and optical surveillance systems require human operators to interpret incoming signals. These operators are naturally susceptible to fatigue, cognitive distraction, and environmental noise, which can inevitably lead to missed targets or misidentifications. Machine learning fundamentally solves this human limitation through its mastery of pattern recognition.
When trained on massive, multi-modal datasets containing thousands of acoustic, visual, and electronic signatures, AI-powered military applications perform Automated Target Recognition (ATR) with unparalleled accuracy. AI can effortlessly sift through high-resolution aerial imagery to detect camouflaged installations or analyze individual pixels in a thermal feed to identify microscopic anomalies that indicate an impending ambush or a concealed improvised explosive device (IED). This automation significantly reduces operator workload, drastically increases target identification speed, and allows personnel to transition from mundane raw data analysis to high-level strategic planning and execution.
| Operational Capability | Human Operator Limitations | AI & Machine Learning Enhancements |
|---|---|---|
| Target Identification Speed | Constrained by biological cognitive limits and manual data review. | Near-instantaneous automated target recognition (ATR) across thousands of feeds. |
| Pattern Recognition | Susceptible to fatigue, distraction, and subtle environmental noise. | Relentless, continuous analysis of microscopic visual and acoustic signatures. |
| Data Ingestion | Limited to viewing one or two screens simultaneously. | Simultaneous processing of multi-modal sensor fusion across the entire network. |
| Equipment Monitoring | Reactive maintenance after a failure has occurred in the field. | Proactive, predictive anomaly detection preventing catastrophic failures. |
Predictive Logistics and Asset Maintenance
The transformative applications of machine learning extend far beyond kinetic threat detection on the battlefield. Maintaining the operational readiness of complex C5ISR assets is a monumental logistical challenge that directly impacts mission success. Predictive maintenance algorithms constantly monitor the health of aircraft, tactical ground vehicles, and communication arrays.
By analyzing real-time telemetry data, these systems detect microscopic anomalies in engine vibrations, fluid pressures, or internal network traffic routing. The AI alerts maintenance crews to potential failures well before they manifest as operational breakdowns in a combat zone. Identifying and rectifying small mechanical or software problems before they cascade into catastrophic failures provides a massive cost benefit and ensures that critical ISR platforms remain operational, secure, and ready for deployment. Looking toward the future of sustainment, predictive logistics will create highly responsive supply networks that dynamically adjust to real-time battlefield conditions, automatically rerouting supplies, anticipating fuel consumption rates, and repositioning personnel to meet forecasted operational demands.
What Role Does AI Play in Military Cybersecurity and Cognitive Electronic Warfare?
How does artificial intelligence enhance military cybersecurity and electronic warfare capabilities? AI-driven cybersecurity tools establish baselines of normal network behavior to continuously monitor traffic, instantly flagging deviations like malware injections and initiating defensive protocols in milliseconds to support Zero Trust Architectures. Concurrently, Cognitive Electronic Warfare uses AI to analyze novel enemy radar signals on the fly, instantly generating custom countermeasures to jam or spoof adversary networks.
The “Cyber” component of C5ISR is arguably the most vulnerable and consistently targeted domain in modern hybrid warfare. As defense systems become increasingly interconnected via the Internet of Military Things (IoMT), the attack surface expands exponentially. Threat actors continuously utilize AI to create automated ransomware distributions and advanced phishing tactics, circumventing traditional security perimeters. AI cybersecurity tools are therefore essential for monitoring network traffic at a scale and speed impossible for human IT security teams.
Accelerating Threat Detection and Zero Trust Architecture
AI has fundamentally altered the timeline of cyber defense. Historically, the duration a threat actor remained undetected inside a network—known as “dwell time”—was dangerously high. Due to AI-enabled predictive analytics and continuous monitoring, average network dwell times have plummeted from 243 days in 2012 to merely 11 days by 2024.
By 2026, the implementation of Zero Trust Architecture (ZTA) across defense networks has moved from a conceptual future mandate to an operational reality. Agencies have shifted away from traditional perimeter-based security toward identity-first, segmented, and continuously validated networks. AI is the core engine that makes continuous authorization possible under ZTA principles. It evaluates user and device behavior in real-time, instantly isolating threats and initiating defensive protocols in milliseconds, effectively halting lateral movement by adversaries within the network.
The Convergence of Cyber and Cognitive Electronic Warfare
In the modern battlespace, cybersecurity and Electronic Warfare (EW) are rapidly converging into a unified spectrum dominance strategy. Cognitive Electronic Warfare utilizes AI to analyze enemy radar and communication signals dynamically. Instead of relying on static, pre-programmed threat libraries that quickly become obsolete against adaptive enemies, cognitive systems analyze novel adversarial emissions on the fly. They instantly generate new, customized countermeasures to jam, spoof, or evade enemy networks.
This dynamic adaptability represents a critical battlefield advantage. Systems like L3Harris’s Distributed Spectrum Collaboration and Operations (DiSCO), when integrated with mission-autonomy software, successfully demonstrate how unmanned systems can detect, analyze, and respond to complex electromagnetic threats without human intervention. These advanced systems gather threat intelligence to create a fused COP of the electromagnetic spectrum, allowing AI-powered assets to autonomously identify safe operating zones and execute tactical maneuvers, ensuring spectrum dominance is maintained even in highly contested, anti-access/area denial (A2/AD) environments.
How is MAG Leading the Next Generation of C5ISR Integration?
What is MAG’s role in the development and integration of AI-driven C5ISR platforms? MAG acts as a premier global provider of full-spectrum ISR services, serving as a primary integrator for critical U.S. Army projects. By partnering on next-generation deep-sensing platforms such as ATHENA-R, MAG specializes in integrating AI, multi-domain sensor fusion, and edge computing into contractor-owned, contractor-operated aircraft to deliver actionable intelligence.
To maintain a decisive advantage over near-peer adversaries, military organizations increasingly partner with specialized defense contractors who possess deep operational expertise in the tactical requirements of C5ISR alongside the technical mastery of artificial intelligence. MAG, headquartered in Fairfax, Virginia, has firmly established itself as a central, indispensable player in this domain.
Founded in 2009 and backed by significant private equity investment, MAG has grown into a premier global provider of manned and unmanned ISR operation, training, and technical maintenance. With over 1,300 personnel and deep integration into federal defense architecture, the company has transitioned from providing traditional aerial surveillance to acting as a sophisticated technology integration firm. MAG focuses heavily on developing innovative solutions that deliver complex, multi-domain data directly to combatant commanders, enabling real-time situational awareness that makes the world smaller and safer.
Under the leadership of executives with deep military and technological backgrounds, MAG consistently secures mission-critical contracts by demonstrating an exceptional performance history of delivering turnkey aerial C5ISR programs in the most austere and challenging operational environments worldwide.
ATHENA-R and Deep Sensing Capabilities
MAG, in a strategic teaming partnership with L3Harris Technologies, was awarded a highly competitive contract to deliver two enhanced ISR aircraft for the Army’s Theater-Level, High-Altitude Expeditionary Next Airborne ISR-Radar program (ATHENA-R). The physical architecture of the ATHENA-R platform relies on a modified Bombardier Global 6500 profile.
This commercial business jet is specifically engineered and militarized to house advanced synthetic aperture radar and moving target indicator (SAR/MTI) radar pods on its underbelly, allowing it to track ground movements with extreme precision through adverse weather and cloud cover. Furthermore, the aircraft is equipped with beyond-line-of-sight (BLOS) communications links and powerful onboard AI edge processing nodes, ensuring data can be analyzed locally and transmitted securely to combatant commands globally.
Operating at altitudes up to 70,000 feet, the ATHENA-R platform provides greater endurance, massive payload capacity, and significantly longer standoff ranges compared to legacy fleets. This deep-sensing capability provides the Army with electronic order of battle mapping and long-range precision fire targeting intelligence without placing the aircraft in immediate kinetic danger.
As Joseph Reale, CEO of MAG, articulated, current geopolitical circumstances demand an adaptable ISR solution capable of addressing near-peer threats, and the ATHENA-R program directly validates the industry’s ability to execute this mission.
How Do Proprietary Mission Management Systems Create a Common Operating Picture?
What technologies are used to unify disjointed intelligence data into a single operational view? Proprietary Mission Management Systems (MMS) utilize AI, augmented reality, and data fusion to aggregate high-resolution imagery, electronic signals, and topographic charts into a single Common Operating Picture (COP). Strategic partnerships, such as MAG’s collaborations with SAS, further enhance these systems by integrating generative AI and edge analytics to rapidly process vast amounts of telemetry.
Modern intelligence gathering relies heavily on sophisticated software architectures capable of unifying highly disjointed and siloed data streams. Proprietary Mission Management Systems—frequently enhanced by AI and augmented reality interfaces such as AIRSCAPE—integrate high-resolution aerial imagery, topographic charts, and AI-assisted target recognition algorithms directly into a single, cohesive interface.
This holistic Common Operating Picture allows mission commanders to synthesize various inputs simultaneously. For example, operators can view Visual Detection and Ranging (ViDAR) feeds alongside stabilized electro-optical camera outputs, optimizing search and rescue operations or lethal target acquisition protocols by calculating threat levels based on fused patterns of life.
Strategic AI Partnerships Expanding the C5ISR Ecosystem
Recognizing that artificial intelligence is not a monolithic technology but a complex ecosystem requiring varied expertise, leading integrators actively cultivate strategic partnerships to expand their capabilities.
- Space Force and SAS Integration: Operating in the extra-terrestrial domain, MAG partnered with SAS under a massive $900 million indefinite delivery, indefinite quantity (IDIQ) contract to support U.S. Space Force Space Systems Command. The strategic objective is to apply advanced analytics and AI to the vast amounts of telemetry generated by thousands of space tracking radars and orbital sensors. By securely hosting the SAS Viya platform in a cloud environment, the teaming arrangement provides advanced analytics for Space Command and Control (C2), converting raw sensor proliferation into highly usable, real-time intelligence for orbital defense.
Furthermore, MAG’s selection for the C5ISR Worldwide-Defense-System Integration, Prototyping, and Security (C-WIPS) task order reinforces their position as a leading systems integrator, providing continuous engineering and prototyping support to the Army Combat Capabilities Development Command.
What is the Future Outlook for Joint All-Domain Command and Control (JADC2)?
How will JADC2 and autonomous technologies shape the future of military operations? The Joint All-Domain Command and Control (JADC2) initiative aims to unify data feeds across all military branches into a single, AI-driven network. This interconnected architecture will enable the deployment of autonomous drone swarms and agentic AI, allowing unmanned systems to self-coordinate, adapt to enemy tactics, and execute complex operations at machine speed without direct human piloting.
The integration of artificial intelligence into defense operations is already accelerating toward its next evolutionary leap, spearheaded by overarching DoD initiatives like JADC2. The fundamental goal of JADC2 is to dismantle the historic communication silos existing between the Air Force, Army, Marine Corps, Navy, and Space Force, connecting sensors from all branches into a single, unified data fabric.
Artificial intelligence military capabilities form the absolute backbone of this project. The JADC2 system utilizes machine learning to sift through joint data feeds, rapidly identifying targets and recommending the most appropriate, available asset to engage them, regardless of which military branch technically owns the kinetic asset.
Programs like Project Maven, originally launched in 2017 to automate the processing of drone video feeds, established the critical foundation for integrating commercial AI technology into tactical military applications. Today’s sophisticated iterations, such as Maven Smart Systems, help military planners identify and prioritize thousands of targets, dramatically accelerating intelligence analysis and creating a seamless continuum from edge sensing directly to enterprise targeting.
Looking forward, military technology development is accelerating rapidly toward the deployment of autonomous swarms. These unmanned aerial and ground systems will communicate seamlessly with one another via secure tactical networks, adapt dynamically to enemy countermeasures, and execute complex, coordinated formations. As AI models transition from simple predictive tools to “agentic” teammates—digital assistants capable of autonomous mission planning and tool execution—the nature of warfare will fundamentally shift toward machine-speed operations.
By leveraging edge computing for zero-latency processing, automating strategic decisions, and deploying state-of-the-art machine learning for threat detection, AI military applications guarantee that allied forces maintain absolute information dominance. To secure this future, continuous, agile partnerships between military organizations and specialized defense contractors like MAG remain the most critical strategic imperative.
Securing the Future of C5ISR
Artificial intelligence is no longer a futuristic concept; it is an active, essential component of modern defense strategy. By leveraging edge computing for real-time processing, automating complex decisions, and deploying machine learning for superior threat detection, AI military applications ensure that forces maintain information dominance.
To stay ahead, military organizations and defense contractors must partner with experts who understand both the tactical requirements of C5ISR and the technical complexities of artificial intelligence.
Are you ready to optimize your C5ISR capabilities with advanced technology? Contact MAG Aerospace today to learn how our experts integrate cutting-edge AI and edge computing solutions into mission-critical defense operations.
Frequently Asked Questions (FAQ)
- What is C5ISR? C5ISR stands for Command, Control, Computers, Communications, Cyber, Intelligence, Surveillance, and Reconnaissance. It describes the integrated architecture of physical systems, digital networks, and operational processes that enable military leaders to communicate seamlessly, gather comprehensive intelligence, and execute informed, data-driven decisions across all domains of warfare.
- How does AI improve C5ISR operations? Artificial intelligence drastically improves C5ISR operations by processing vast volumes of multi-domain data in real time, automating complex decision-making processes, and detecting subtle threats more accurately than traditional human-reliant methods. This technological integration results in sharper situational awareness, compressed OODA loops, and significantly faster kinetic response times on the battlefield.
- What role does edge computing play in military applications? Edge computing allows data to be processed locally at the source of collection, such as directly onboard a drone or tactical ground vehicle, rather than transmitting it to a centralized cloud server. In C5ISR operations, this reduces processing latency, conserves critical bandwidth, and ensures that sensors can continue to deliver actionable insights even in contested environments where communication networks are jammed or disrupted by adversaries.
- How is machine learning used for threat detection in defense? Machine learning algorithms are trained to analyze massive datasets of acoustic, visual, thermal, and cyber signals. Through advanced pattern recognition, they identify threats, camouflage, and tactical anomalies that might easily go unnoticed by human operators experiencing cognitive fatigue. ML is also extensively utilized for predictive maintenance, anticipating equipment and vehicle failures before they occur in the field.
- Can military AI systems make decisions without human input? While military AI applications can process massive datasets, model complex scenarios, and recommend optimized courses of action autonomously, they are fundamentally designed to assist and augment human operators rather than fully replace them. In lethal targeting and strategic command scenarios, critical decisions and the final authorization to act remain firmly with human leaders, adhering strictly to the principle of a human-machine decision-making continuum.
- What is the OODA Loop, and how does AI affect it? The OODA Loop (Observe, Orient, Decide, Act) is a core strategic framework for military decision-making. AI compresses this cycle by automating the observation of data across the battlespace, using machine learning to instantly orient the commander to tactical realities, and generating predictive models for decision support. This allows allied forces to execute the “Act” phase significantly faster than adversaries who rely solely on manual human analysis.
- What is Cognitive Electronic Warfare? Cognitive Electronic Warfare refers to the use of artificial intelligence to dynamically analyze enemy radar and communication signals on the fly. Instead of relying on static, pre-existing databases of known threats, cognitive EW systems instantly generate novel countermeasures to jam, spoof, or evade adversary networks, ensuring forces maintain spectrum dominance in real time.